What are the configuration steps to enable DKIM signing for outbound messages on FortiMail? (Choose three.)
Which firmware upgrade method for an active-passive HA cluster ensures service outage is minimal, and there are no unnecessary failovers?
Refer to the exhibit.
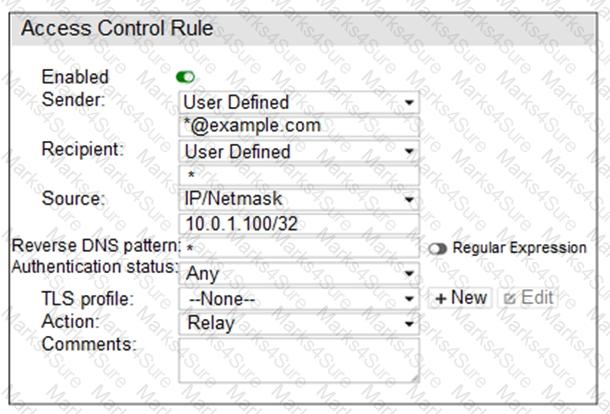
Which two statements about the access receive rule are true? (Choose two.)
Examine the FortiMail antivirus action profile shown in the exhibit; then answer the question below.
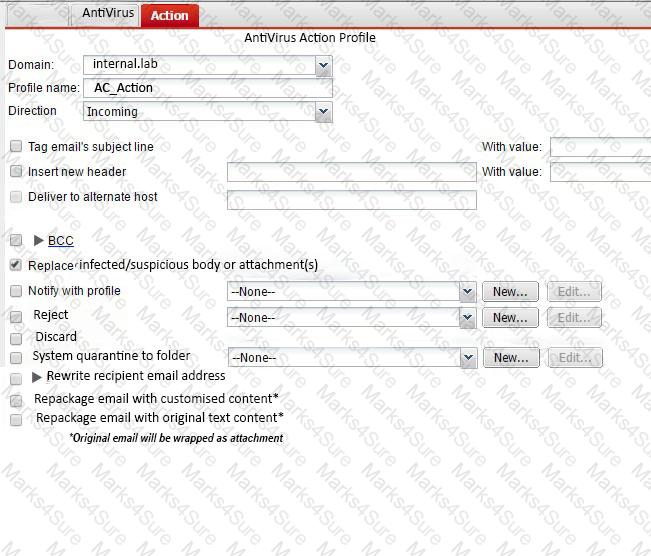
What is the expected outcome if FortiMail applies this action profile to an email? (Choose two.)
Examine the FortiMail recipient-based policy shown in the exhibit; then answer the question below.
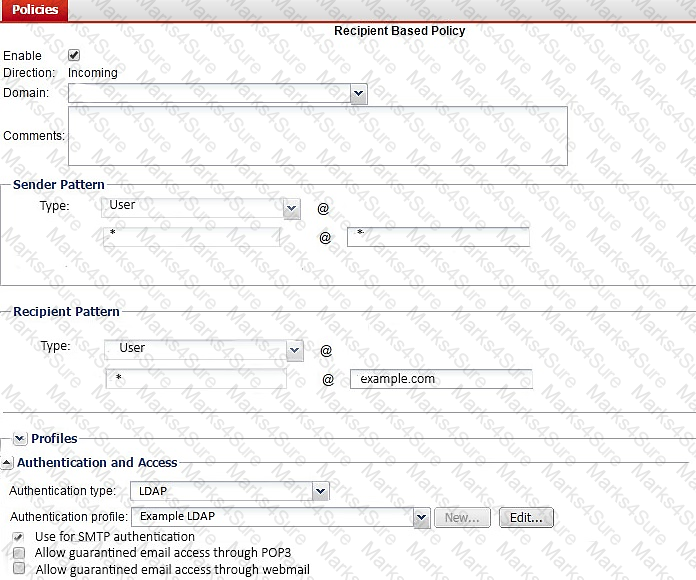
After creating the policy, an administrator discovered that clients are able to send unauthenticated email using SMTP. What must be done to ensure clients cannot send unauthenticated email?
Examine the access receive rule shown in the exhibit; then answer the question below.
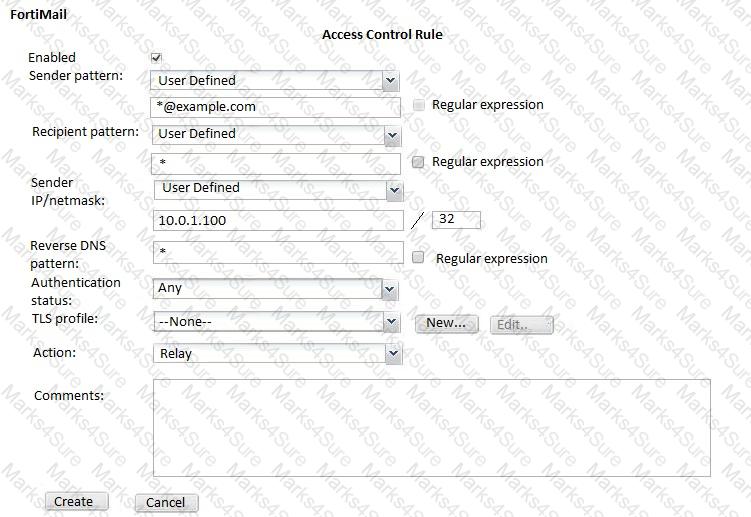
Which of the following statements are true? (Choose two.)
Examine the FortiMail user webmail interface shown in the exhibit; then answer the question below.
Which one of the following statements is true regarding this server mode FortiMail’s configuration?
Which of the following antispam techniques queries FortiGuard for rating information? (Choose two.)
Which of the following statements are true regarding FortiMail’s behavior when using the built-in MTA to process email in transparent mode? (Choose two.)
Refer to the exhibit.

MTA-1 is delivering an email intended for User 1 to MTA-2.
Which two statements about protocol usage between the devices are true? (Choose two.)
Refer to the exhibit.
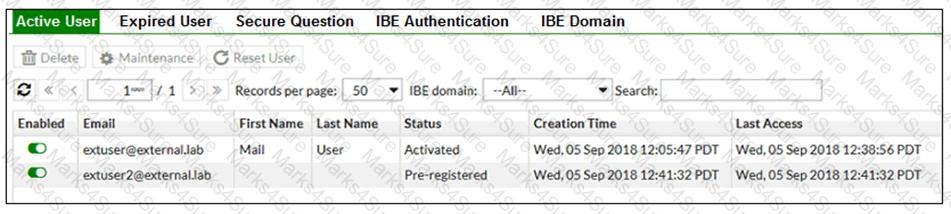
Which statement describes the pre-registered status of the IBE user extuser2@external.lab?
Refer to the exhibit.
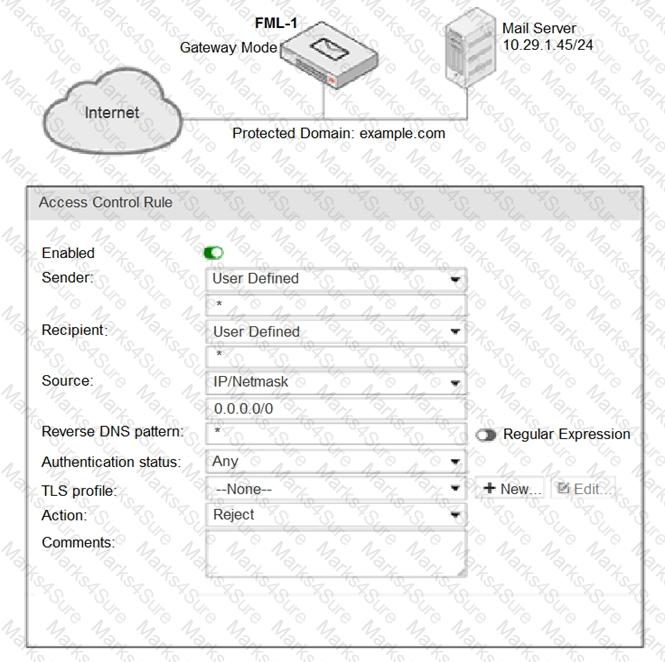
It is recommended that you configure which three access receive settings to allow outbound email from the
example.com domain on FML-1? (Choose three.)
Which FortiMail option removes embedded code components in Microsoft Word, while maintaining the original file format?