NSE6_OTS_AR-7.6 Fortinet NSE 6 - OT Security 7.6 Architect Questions and Answers
In the Purdue model, at which level are physical assets like the Industrial Internet of Things (IIoT) placed? (Choose one answer)
Refer to the exhibit.
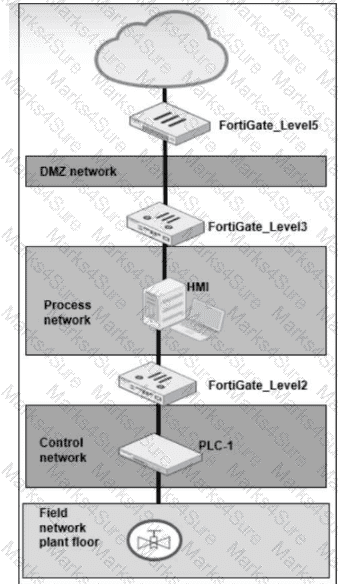
A simplified OT network is shown. You want to optimize the protection of this OT network. Which two controls must you implement? (Choose two answers)
You want to improve the security of your OT network and therefore deploy a FortiGate device with the OT signatures database. Which two statements about this database are true? (Choose two answers)
You want FortiAnalyzer to trigger an automation stitch on a FortiGate device automatically. What must you configure on FortiAnalyzer to enable direct communication with FortiGate? (Choose one answer)
Refer to the exhibit.
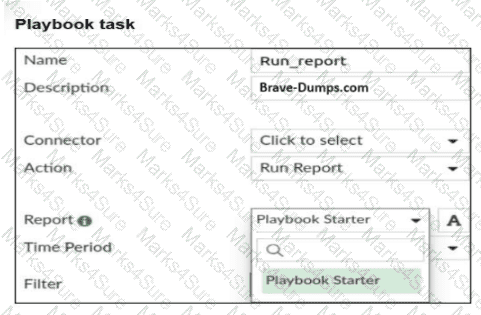
A Run_report task is shown. You want to automate the generation of a newly created report on FortiAnalyzer . When you configure the Run_report task in Playbook, why is the report not shown in the Report field? (Choose two answers)
Refer to the exhibit.
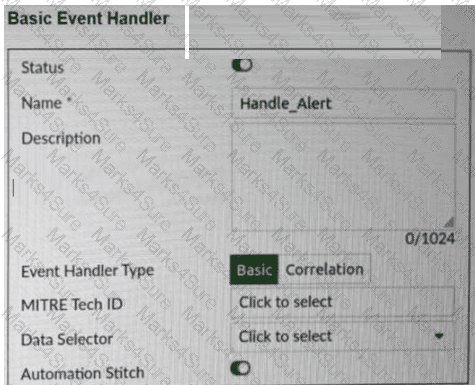
A basic event handler is shown. You have enabled Automation Stitch to automate the handling of an alert. Which two steps must you take to use this automation stitch? (Choose two answers)
Refer to the exhibits.
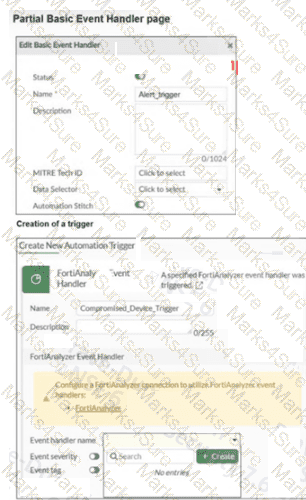
A partial Basic Event Handler page on FortiAnalyzer and the creation of a trigger in a FortiGate device are shown. To improve the protection of your OT network, you want to automate the handling of compromised devices notified through FortiAnalyzer. You have configured an event handler named Alert_trigger as shown in the exhibit. When you create the trigger on the FortiGate device, the Event handler name field does not provide the Alert_trigger option. What two actions must you perform to make the Alert_trigger option available? (Choose two answers)
Refer to the exhibit.
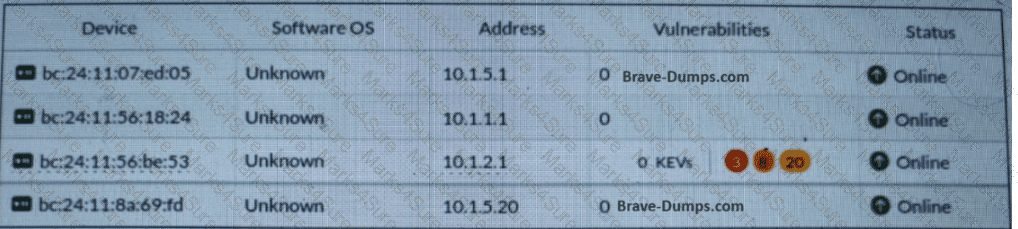
Which statement about this partial Asset Identity List page is correct? (Choose one answer)
Refer to the exhibit.
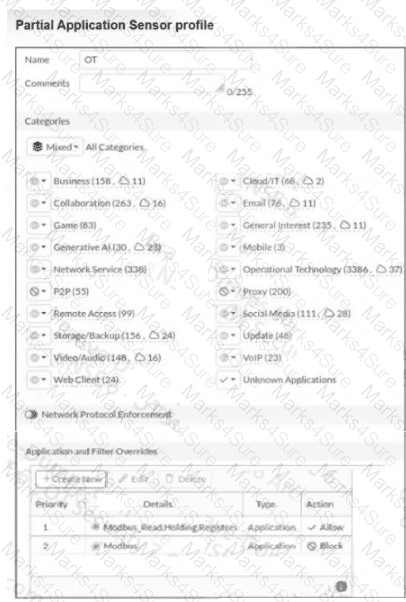
A partial Application Sensor profile is shown. When you apply this profile in firewall policy, which two statements are correct? (Choose two answers)
During layer 2 polling , which two pieces of information are gathered by FortiNAC to identify a device? (Choose two answers)


