NSE7_SSE_AD-25 Fortinet NSE 7 - FortiSASE 25 Enterprise Administrator Questions and Answers
Refer to the exhibits.
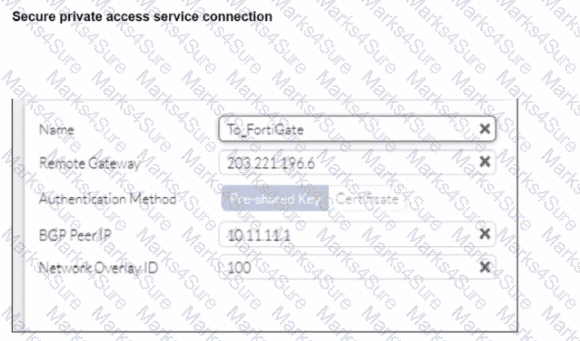
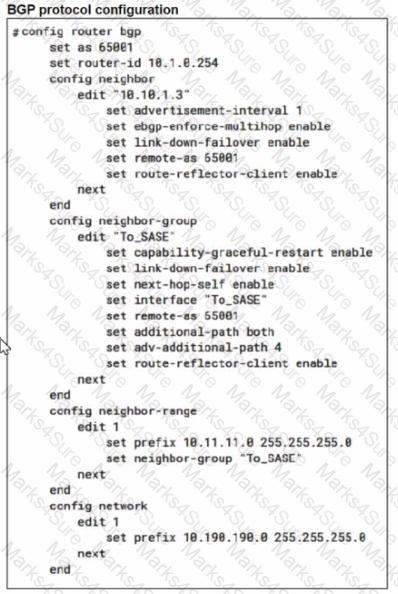
A FortiSASE administrator is trying to configure FortiSASE as a spoke to a FortiGate hub. The VPN tunnel does not establish
Based on the provided configuration, what configuration needs to be modified to bring the tunnel up?
What are two benefits of deploying secure private access (SPA) with SD-WAN? (Choose two answers)
Refer to the exhibit.
To allow access, which web tiller configuration must you change on FortiSASE?
Refer to the exhibit.
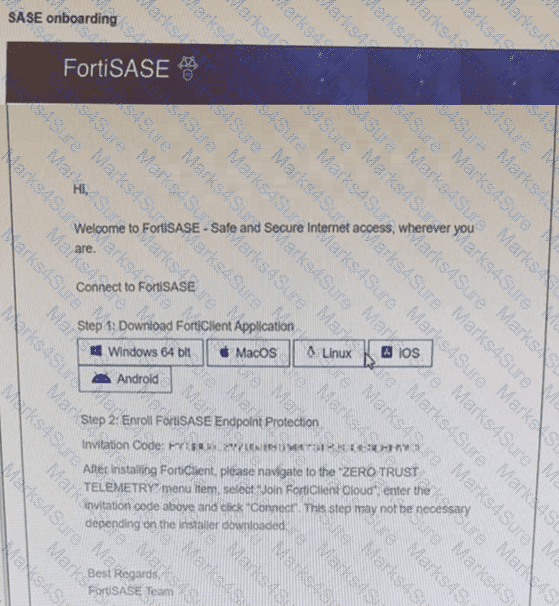
Which two statements about the onboarding process shown in the exhibit are true? (Choose two answers)
How does FortiSASE Secure Private Access (SPA) facilitate connectivity to private resources in a hub-and-spoke network? (Choose one answer)
Refer to the exhibits.
WiMO-Pro and Win7-Pro are endpoints from the same remote location. WiMO-Pro can access the internet though FortiSASE, while Wm7-Pro can no longer access the internet
Given the exhibits, which reason explains the outage on Wm7-Pro?
What action must a FortiSASE customer take to restrict organization SaaS access to only FortiSASE-connected users? (Choose one answer)
Which two benefits come from integrating SoCaaS with FortiSASE? (Choose two answers)
When you configure FortiSASE Secure Private Access (SPA) with SD-WAN integration, you must establish a routing adjacency between FortiSASE and the FortiGate SD-WAN hub. Which routing protocol must you use?
Which role does FortiSASE play in supporting zero trust network access (ZTNA) principles9
Refer to the exhibits.
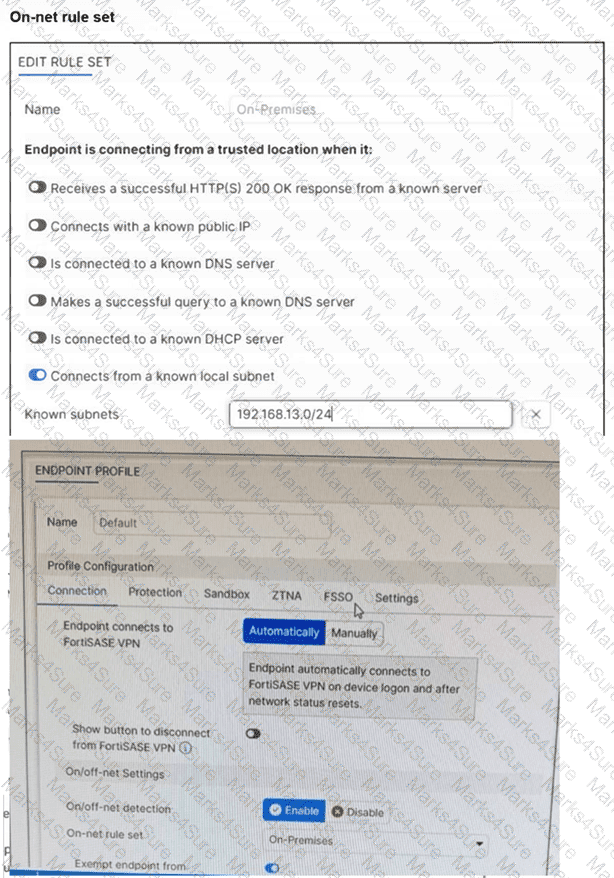
An endpoint is assigned an IP address of 192.168.13.101/24. Which action will be run on the endpoint? (Choose one answer)
Refer to the exhibit.
In the user connection monitor, the FortiSASE administrator notices the user name is showing random characters. Which configuration change must the administrator make to get proper user information?
Which three traffic flows are supported by FortiSASE Secure Private Access (SPA)? (Choose three answers)
You are designing a new network for Company X and one of the new cybersecurity policy requirements is that all remote user endpoints must always be connected and protected Which FortiSASE component facilitates this always-on security measure?
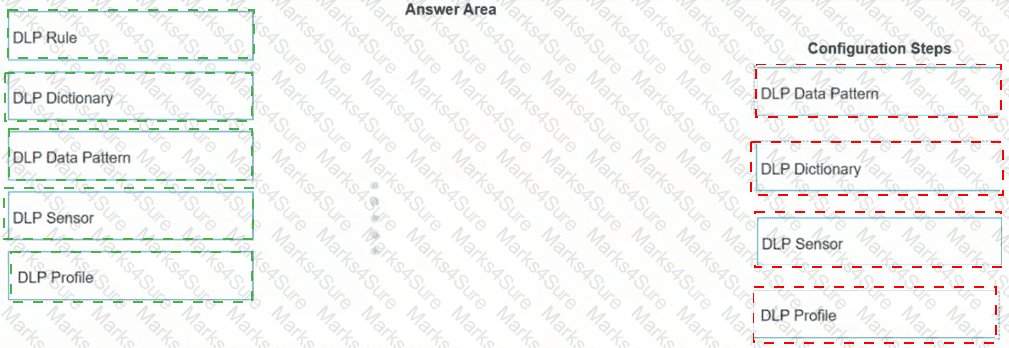
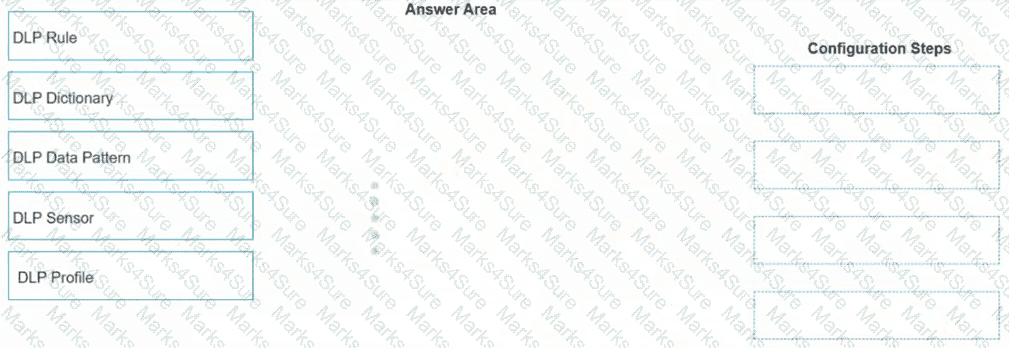
When configuring the DLP rule in FortiSASE using Regex format, what would be the correct order for the configuration steps? (Place the four correct steps in order)
Refer to the exhibits.
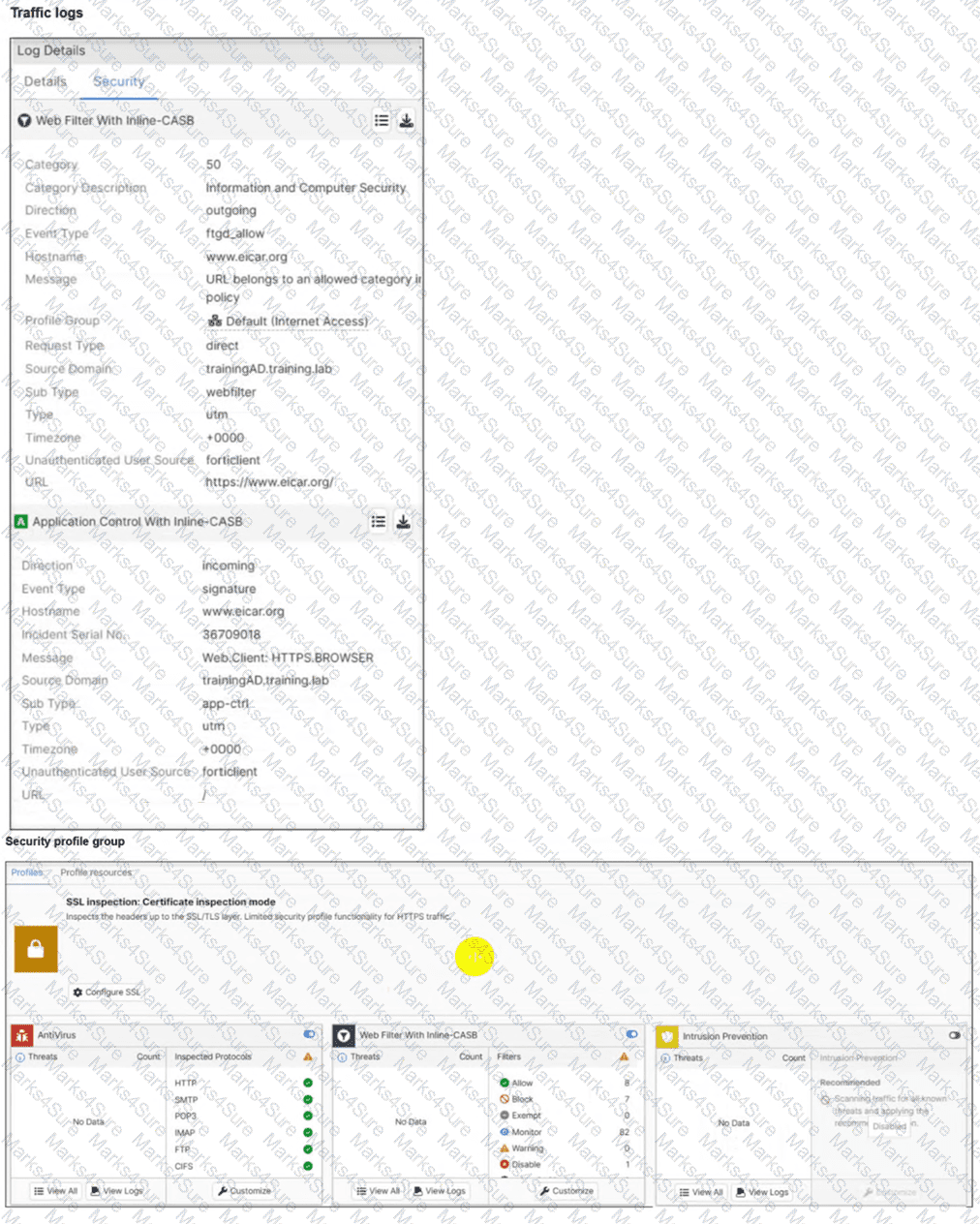
A FortiSASE administrator has configured an antivirus profile in the security profile group and applied it to the internet access policy. Remote users are still able to download the eicar.com-zip file from https://eicar.org.
Which configuration on FortiSASE is allowing users to perform the download? (Choose one answer)
Which information does FortiSASE use to bring network lockdown into effect on an endpoint? (Choose one answer)
To complete their day-to-day operations, remote users require access to a TCP-based application that is hosted on a private web server. Which FortiSASE deployment use case provides the most efficient and secure method for meeting the remote users ' requirements?
What is the purpose of the grace period for off-net endpoints in the FortiSASE Network Lockdown feature? (Choose one answer)
Which FortiSASE feature ensures least-privileged user access to all applications?