You want to prevent a document stored in Google Drive from being shared externally with a public link. What would you configure in Netskope to satisfy this requirement?
Which statement describes how Netskope ' s REST API, v1 and v2, handles authentication?
You are deploying a Netskope client in your corporate office network. You are aware of firewall or proxy rules that need to be modified to allow traffic.
Which two statements are true in this scenario? (Choose two.)
Your small company of 10 people wants to deploy the Netskope client to all company users without requiring users to be imported using Active Directory, LDAP, or an IdP.
The risk team at your company has determined that traffic from the sales team to a custom Web application should not be inspected by Netskope. All other traffic to the Web application should continue to be inspected. In this scenario, how would you accomplish this task?
Your company is using on-premises QRadar as a SIEM solution. They are replacing it with Rapid7 in the cloud. The legacy on-premises QRadar will eventually be decommissioned. Your IT department does not want to use the same token that QRadar uses.
Your company asks you to use Netskope to integrate with Endpoint Detection and Response (EDR) vendors such as Crowdstrike.
Which two requirements are needed for a successful integration and sharing of threat data? (Choose two.)
You have created a specific Skope IT application events query and want to have the query automatically run and display the results every time you log into your tenant.
Which two statements are correct in this scenario? (Choose two.)
You are testing policies using the DLP predefined identifier " Card Numbers (Major Networks; all). " No DLP policy hits are observed.
Netskope support advised you to enable DTLS for belter performance. You added firewall rules to allow UDP port 443 traffic. These settings are part of which configuration element when enabled in the Netskope tenant?
A city uses many types of forms, including permit applications. These forms contain personal and financial information of citizens. Remote employees download these forms and work directly with the citizens to complete them. The city wants to be able to identify and monitor the specific forms and block the employees from downloading completed forms.
Which feature would you use to accomplish this task?
Review the exhibit.
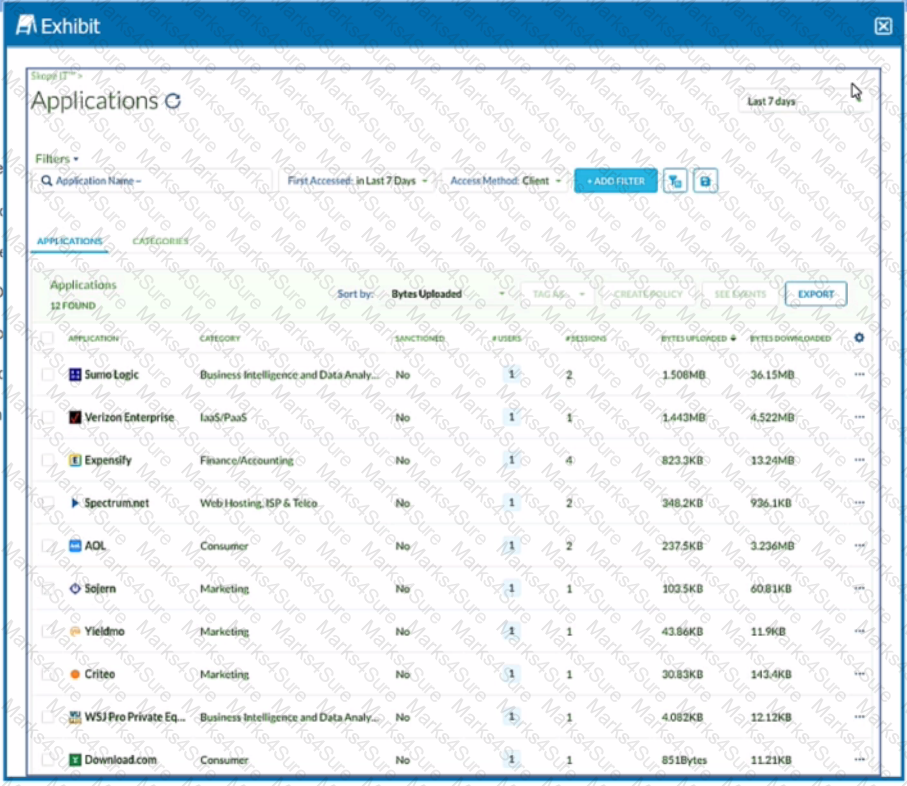
You want to discover new cloud applications in use within an organization.
Referring to the exhibit, which three methods would accomplish this task? (Choose three.)
Review the exhibit.
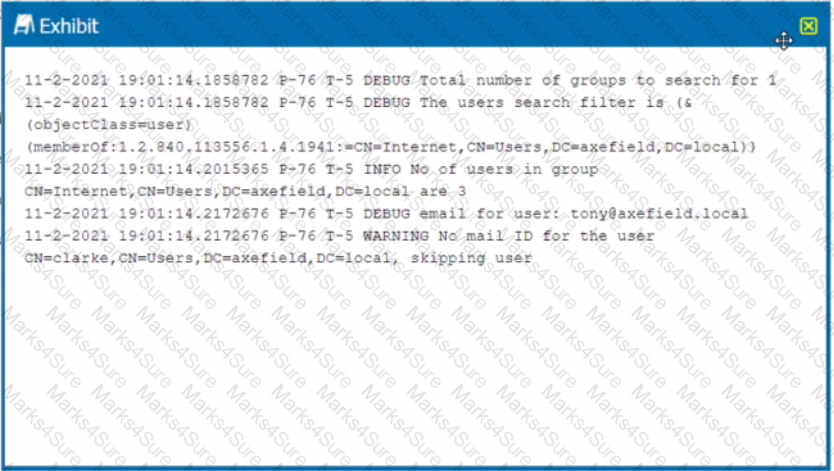
You are troubleshooting a Netskope client for user Clarke which remains in a disabled state after being installed. After looking at various logs, you notice something which might explain the problem. The exhibit is an excerpt from the nsADImporterLog.log.
Referring to the exhibit, what is the problem?
You want the ability to perform automated remediation of misconfigurations on GitHub, Microsoft 365, Salesforce, ServiceNow, and Zoom.
You are provisioning Netskope users from Okta with SCIM Provisioning, and users are not showing up in the tenant. In this scenario, which two Netskope components should you verify first In Okta for accuracy? (Choose two.)
Your customer implements Netskope Secure Web Gateway to secure all Web traffic. While they have created policies to block certain categories, there are many new sites available dally that are not yet categorized. The customer ' s users need quick access and cannot wait to put in a request to gain access requiring a policy change or have the site ' s category changed.
To solve this problem, which Netskope feature would provide quick, safe access to these types of sites?
You want to provide malware protection for all cloud storage applications.
In this scenario, which action would accomplish this task?
Review the exhibit.
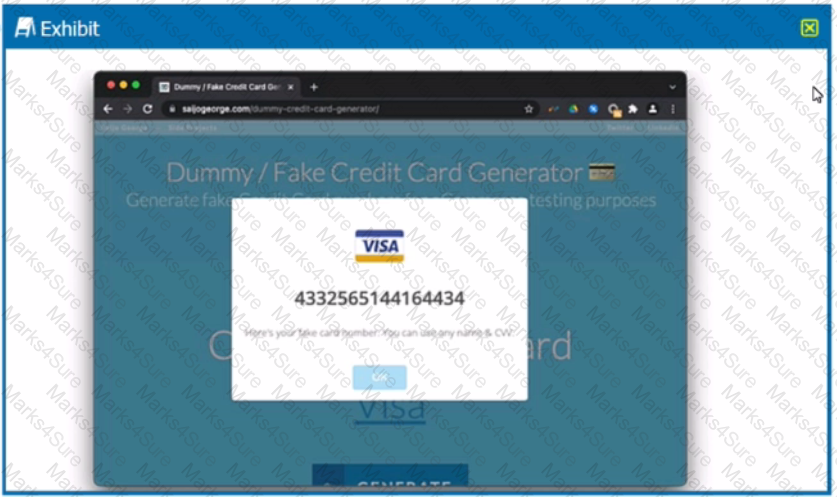
You are asked to create a DLP profile that will ensure that the data shown in the exhibit cannot be uploaded to a user ' s personal Google Drive.
What must be used to accomplish this task?
Your company wants to know if there has been any unusual user activity. In the UI, you go to Skope IT - > Alerts.
Which two types of alerts would you filter to find this information? (Choose two.)
Your IT organization is migrating its user directory services from Microsoft Active Directory to a cloud-based Identity Provider (IdP) solution, Azure AD. You are asked to adapt the Netskope user provisioning process to work with this new cloud-based IdP.
With Netskope DLP, which feature would be used to detect keywords such as " Confidential " or " Access key " ?
Review the exhibit.
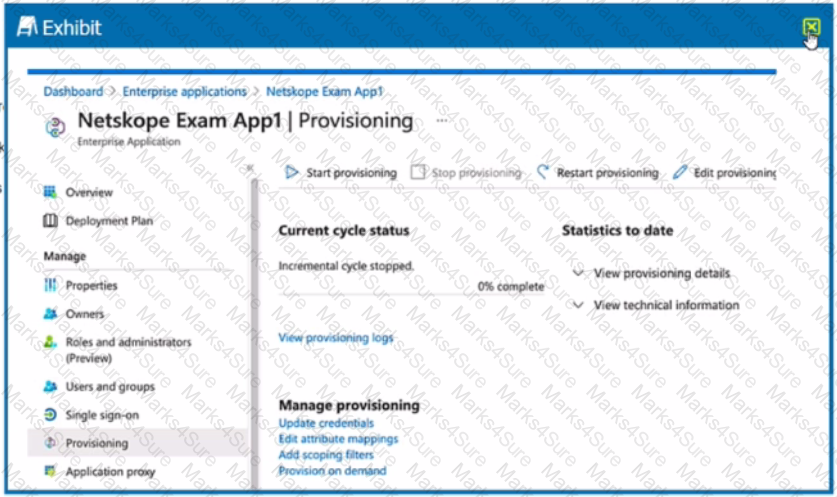
What is the purpose of the configuration page shown Ii the exhibit?
Your company wants to deploy Netskope using a tunnel because you have a mixture of device operating systems. You also do not want to enable encryption because you want to maximize bandwidth.
You want to provision users and groups to a Netskope tenant. You have Microsoft Active Directory servers hosted in two different forests. Which statement is true about this scenario?