Which Cyber Are components or products can be used to discover Windows Services or Scheduled Tasks that use privileged accounts? Select all that apply.
Which statement is true about setting the reconcile account at the platform level?
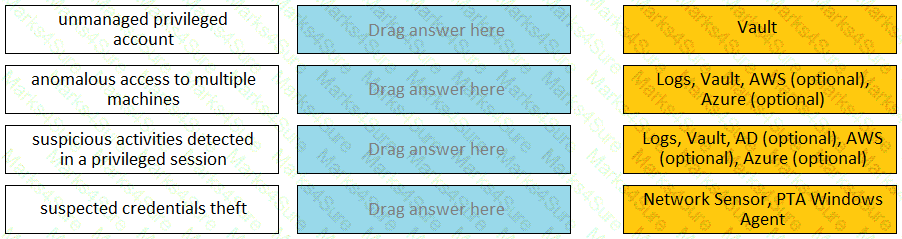
Match each PTA alert category with the PTA sensors that collect the data for it.
When running a “Privileged Accounts Inventory” Report through the Reports page in PVWA on a specific safe, which permission/s are required on that safe to show complete account inventory information?
You have associated a logon account to one your UNIX cool accounts in the vault. When attempting to [b]change [/b] the root account’s password the CPM will…..
Which command configures email alerts within PTA if settings need to be changed post install?
Assuming a safe has been configured to be accessible during certain hours of the day, a Vault Admin may still access that safe outside of those hours.
A user needs to view recorded sessions through the PVWA.
Without giving auditor access, which safes does a user need access to view PSM recordings? (Choose two.)
Which keys are required to be present in order to start the PrivateArk Server service?
A newly created platform allows users to access a Linux endpoint. When users click to connect, nothing happens.
Which piece of the platform is missing?
It is possible to control the hours of the day during which a user may log into the vault.
In your organization the “click to connect” button is not active by default.
How can this feature be activated?
Which of the following properties are mandatory when adding accounts from a file? (Choose three.)
When a DR Vault Server becomes an active vault, it will automatically fail back to the original state once the Primary Vault comes back online.
What is the maximum number of levels of authorization you can set up in Dual Control?
Which CyberArk utility allows you to create lists of Master Policy Settings, owners and safes for output to text files or MSSQL databases?
Which type of automatic remediation can be performed by the PTA in case of a suspected credential theft security event?
You have been asked to turn off the time access restrictions for a safe.
Where is this setting found?
Which built-in report from the reports page in PVWA displays the number of days until a password is due to expire?
What is the correct process to install a custom platform from the CyberArk Marketplace?
A user with administrative privileges to the vault can only grant other users privileges that he himself has.
Which service should NOT be running on the DR Vault when the primary Production Vault is up?
Your customer, ACME Corp, wants to store the Safes Data in Drive D instead of Drive C.
Which file should you edit?
What is the configuration file used by the CPM scanner when scanning UNIX/Linux devices?
You are concerned about the Windows Domain password changes occurring during business hours.
Which settings must be updated to ensure passwords are only rotated outside of business hours?
PSM for Windows (previously known as “RDP Proxy”) supports connections to the following target systems
By default, members of which built-in groups will be able to view and configure Automatic Remediation and Session Analysis and Response in the PVWA?
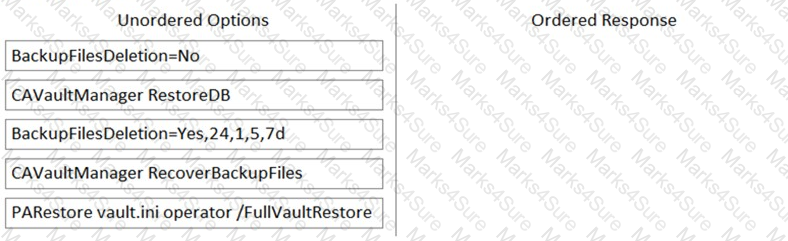
Arrange the steps to restore a Vault using PARestore for a Backup in the correct sequence.
In accordance with best practice, SSH access is denied for root accounts on UNIX/LINUX system. What is the BEST way to allow CPM to manage root accounts.
Users can be resulted to using certain CyberArk interfaces (e.g.PVWA or PACLI).
It is possible to restrict the time of day, or day of week that a [b]verify[/b] process can occur
You notice an authentication failure entry for the DR user in the ITALog.
What is the correct process to fix this error? (Choose two.)
Users who have the ' Access Safe without confirmation ' safe permission on a safe where accounts are configured for Dual control, still need to request approval to use the account.
A new HTML5 Gateway has been deployed in your organization.
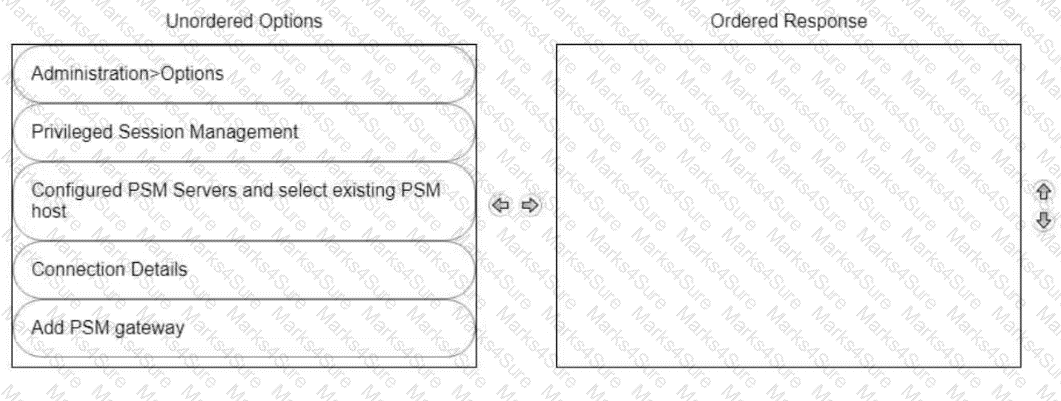
From the PVWA, arrange the steps to configure a PSM host to use the HTML5 Gateway in the correct sequence.
You are onboarding an account that is not supported out of the box.
What should you do first to obtain a platform to import?
To ensure all sessions are being recorded, a CyberArk administrator goes to the master policy and makes configuration changes.
Which configuration is correct?
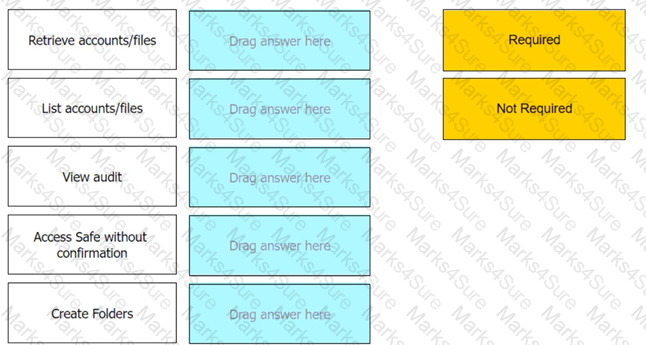
Which authorizations are required in a recording safe to allow a group to view recordings?
Which change could CyberArk make to the REST API that could cause existing scripts to fail?
When a DR Vault Server becomes an active vault, it will automatically revert back to DR mode once the Primary Vault comes back online.
You are configuring CyberArk to use HTML5 gateways exclusively for PSM connections.
In the PVWA, where do you set DefaultConnectionMethod to HTML5?
As long as you are a member of the Vault Admins group, you can grant any permission on any safe that you have access to.
When an account is unable to change its own password, how can you ensure that password reset with the reconcile account is performed each time instead of a change?
You want to build a connector that connects to a website through the Web applications for PSM framework.
Which default connector do you duplicate and modify?
Where can a user with the appropriate permissions generate a report? (Choose two.)
A new colleague created a directory mapping between the Active Directory groups and the Vault.
Where can the newly Configured directory mapping be tested?
Your organization requires all passwords be rotated every 90 days.
Where can you set this regulatory requirement?
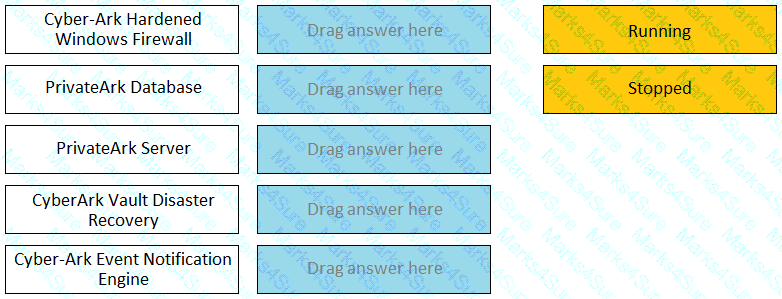
Match the Status of Service on a DR Vault to what is displayed when it is operating normally in Replication mode.
What is required to enable access over SSH to a Unix account through both PSM and PSMP?
A recently-hired colleague onboarded five new Local Accounts that are used for five standalone Windows Servers. After attempting to connect to the servers from PVWA, the colleague noticed that the " Connect " button was greyed out for all five new accounts.
What can you do to help your colleague resolve this issue? (Choose two.)
In the Private Ark client under the Tools menu > Administrative Tools > Users and Groups, which option do you use to update users’ Vault group memberships?
PTA can automatically suspend sessions if suspicious activities are detected in a privileged session, but only if the session is made via the CyberArk PSM.