You have been hired to consult with storage administrators that are working with zoning and naming convention consistency issues. There are numerous types of zoning methods available using standards that also include aliasing. You want to use a method that guarantees unique global port identification.
What accomplishes this goal?
Click the Exhibit button.
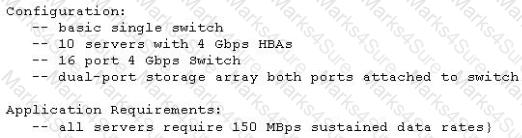
Referring to the configuration shown in the exhibit, when will the servers oversubscribe the connections between the storage array and the switch?
A solution architect needs to know how your switches enforce zoning. The enforcement method and identification type being used in your current FC switches must provide the highest level of security.
Which zoning enforcement should you use?
A colleague asks you if the added cost of using encrypting tape drives and sending the tapes off-site is warranted, since your IT organization already has large security investments such as firewalls and database table encryption.
What is your response?
Click the Exhibit button.
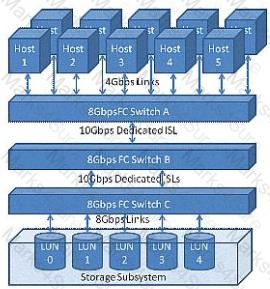
The customer configuration shown in the exhibit is not meeting the throughput needs of a newly installed application. The application's I/O profile consists of 100% 4 kilobyte reads and all servers require a sustained bandwidth of 150 MBps.
Which location within the configuration presents a performance bottleneck?
A company wants to implement a database which requires a storage subsystem with no more than 2 ms write latency and 1 ms read latency.
Which type of drive would you use?
You want to prevent unauthorized switches from connecting to your company's fabrics.
What should you do?
After the storage administrator merged two multi-vendor FC SANs, an error indicates that two ports have become isolated causing a segmentation to exist in the fabric.
Which two events would cause this? (Choose two.)
Click the Exhibit button.
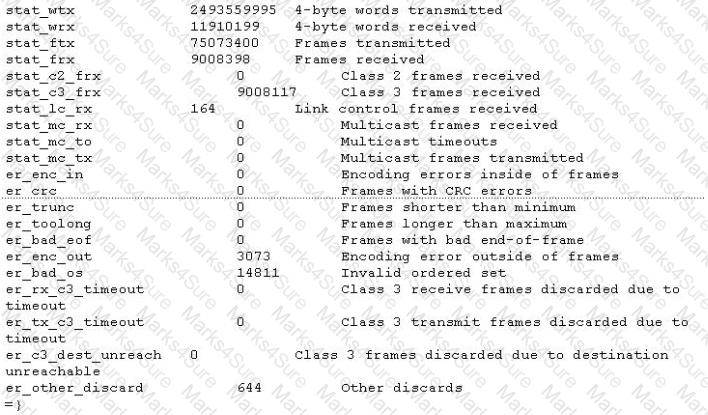
Referring to the exhibit, which three switch indicators will help you to determine the stability of a link? (Choose three.)
You need to add an iSCSI host and storage array to your environment. Your manager wants at least two options that allow all iSCSI initiators to query a central management server to locate the address of all iSCSI resources (e.g., iSCSI initiators, targets, switches, and management stations).
Which two protocol methods would be used? (Choose two.)
Click the Exhibit button.
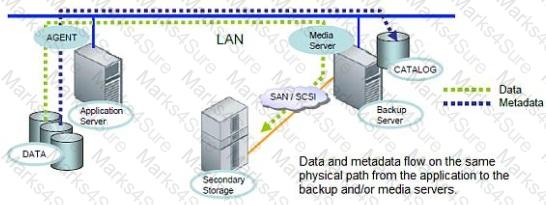
Referring to the exhibit, which backup type is represented?
The CIO would like to segregate management device IP network traffic from server IP network traffic within the data center to limit potential security threats.
What would be used to accomplish this?
The system administrator has received complaints about the decreased performance of two LUNs. When you investigate the port being used to connect to the LUNs, you discover that the port has achieved its maximum throughput. You also discover that there are other ports available on the storage array that are not oversubscribed.
Which specific driver is needed to balance workloads between the host and storage?
Five out of 4S servers using one particular enterprise storage system are experiencing performance degradation during normal working hours. All 48 servers have similar workload characteristics. There are multiple disk groups that make up your enterprise storage.
What should be monitored to determine the root cause?
You have been hired as a consultant to help resolve boot-from-SAN server reboots. The company has hosts, storage devices, and tape drives in the same zones. A large number of RSCNs are generated during the backup window.
What is the cause of the problem?
You need to merge two existing FC fabrics. After connecting the ISL to join the fabrics, numerous switches segment.
What should be done to prevent the segmentation?
You have been asked to secure your FC switches in the data center. Unsecure protocols have already been disabled but you also need to restrict access to the switches only from specific IP addresses located on the production network.
What should be used?
You have been asked to create a LUN on a storage array that is comprised of 7,200 rpm SATA drives. Each drive is rated at 100 IOPS. The LUN should provide a minimum of 1100 IOPS and withstand multiple drive failures using the least number of drives.
How many drives and which RAID level should you use to create this LUN?
Click the Exhibit button.
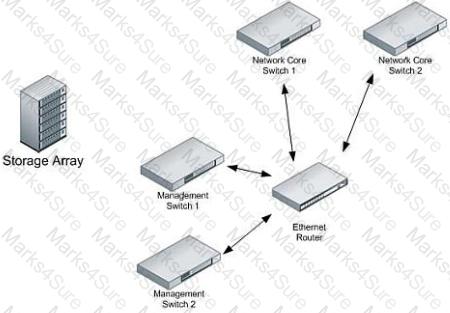
Your company has purchased a new storage array that has dual management access network ports. You need to connect the array and provide maximum redundancy without affecting production traffic.
Referring to the exhibit, where should the ports be attached?
Click the Exhibit button.
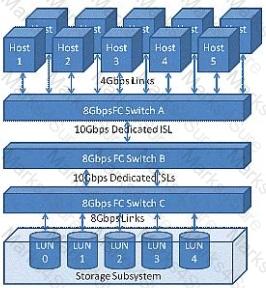
The customer application requires a 50/50 R/W ratio with 100 MBps throughput requirements for each direction of the link. The application servers will simultaneously sustain these data rates across all LUNs in parallel.
Referring to the exhibit, where will the oversubscribed link(s) occur?
You receive a ticket from a database group which is complaining about slow access to storage on only one particular server, as compared to other servers in an active-active cluster. You verify zoning and LUN masking which are fine. On the FC switch, you verify link speed, errors, and throughput for the FC switch ports used by this server. There are no errors on the ports and the link speed is the same as on the switch ports used by other servers in the cluster. You notice that on one port on the FC switch used by this server, that there is no throughput at all.
What is causing the problem?
You have determined that the root cause of your problem is related to invalid characters being intermittently transmitted on your 4 Gb FC link.
What describes this condition?
Your CTO is concerned over misuse of corporate storage assets because an employee was found to be hosting a music library on one of the SANs storage arrays. You have been instructed to provide some level of device security to the corporate FC SAN. FC has a number of cost-effective (free) industry standard protection mechanisms that provide or restrict user access to SAN resources.
Which two FC provided mechanisms would you implement first? (Choose two.)