A Kubernetes application attempting to authenticate to the Follower load balancer receives this error:
ERROR: 2024/10/30 06:07:08 authenticator.go:139: CAKC029E Received invalid response to certificate signing request. Reason: status code 401
When checking the logs, you see this message:
authn-k8s/prd-cluster-01 is not enabled
How do you remediate the issue?
You are setting up a Kubernetes integration with Conjur. With performance as the key deciding factor, namespace and service account will be used as identity characteristics.
Which authentication method should you choose?
What is the most maintenance-free way to ensure a Conjur host’s access reflects any changes made to accounts in a safe in the CyberArk vault?
You modified a Conjur host policy to change its annotations for authentication.
How should you load the policy to make those changes?
When an application is retrieving a credential from Conjur, the application authenticates to Follower A. Follower B receives the next request to retrieve the credential.
What happens next?
When attempting to retrieve a credential, you receive an error 401 – Malformed Authorization Token.
What is the cause of the issue?
While retrieving a secret through REST, the secret retrieval fails to find a matching secret. You know the secret onboarding process was completed, the secret is in the expected safe with the expected object name, and the CCP is able to provide secrets to other applications.
What is the most likely cause for this issue?
A customer wants to ensure applications can retrieve secrets from Conjur in three different data centers if the Conjur Leader becomes unavailable. Conjur Followers are already deployed in each of these data centers.
How should you architect the solution to support this requirement?
You are deploying Kubernetes resources/objects as Conjur identities.
In addition to Namespace and Deployment, from which options can you choose? (Choose two.)
A customer has 100 .NET applications and wants to use Summon to invoke the application and inject secrets at run time.
Which change to the NET application code might be necessary to enable this?
A customer wants to minimize the Kubernetes application code developers must change to adopt Conjur for secrets access.
Which solutions can meet this requirement? (Choose two.)
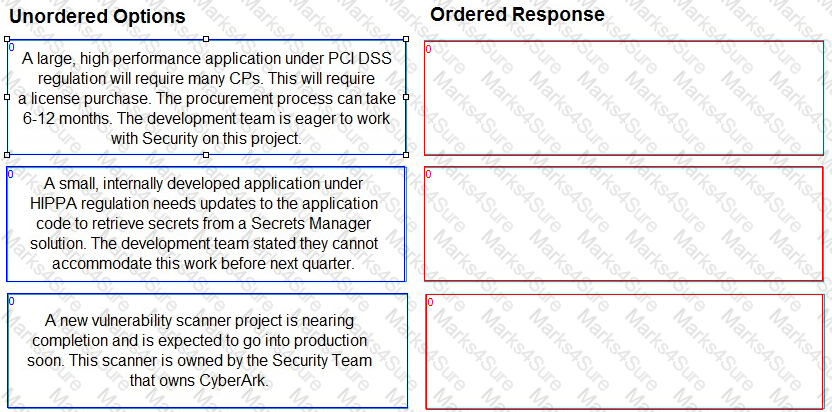
Findings were obtained after cataloging pending Secrets Manager use cases.
Arrange the findings in the correct order for prioritization.