Which of the following applications can help determine whether a denial-of-service attack is occurring against a network host?
A security breach has occurred in which a third party was able to obtain and misuse legitimate authentication information. After investigation, you determined that the specific cause for the breach was that end users have been placing their passwords underneath their keyboards. Which step will best help you resolve this problem?
A new server has been placed on the network. You have been assigned to protect this server using a packet-filtering firewall. To comply with this request, you have enabled the following ruleset:
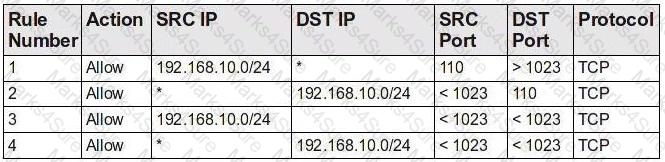
Which choice describes the next step to take now that this ruleset has been enabled?
Which of the following details should be included in documentation of an attack?
Consider the following diagram:
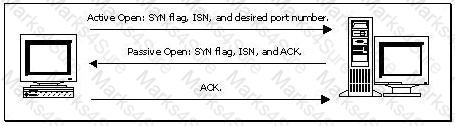
Which of the following best describes the protocol activity shown in the diagram, along with the most likely potential threat that accompanies this protocol?
You have determined that the company Web server has several vulnerabilities, including a buffer overflow that has resulted in an attack. The Web server uses PHP and has direct connections to an Oracle database server. It also uses many CGI scripts. Which of the following is the most effective way to respond to this attack?
Which of the following is the most likely first step to enable a server to recover from a denial-of-service attack in which all hard disk data is lost?
You have implemented a service on a Linux system that allows a user to read and edit resources. What is the function of this service?
Consider the following image of a packet capture:
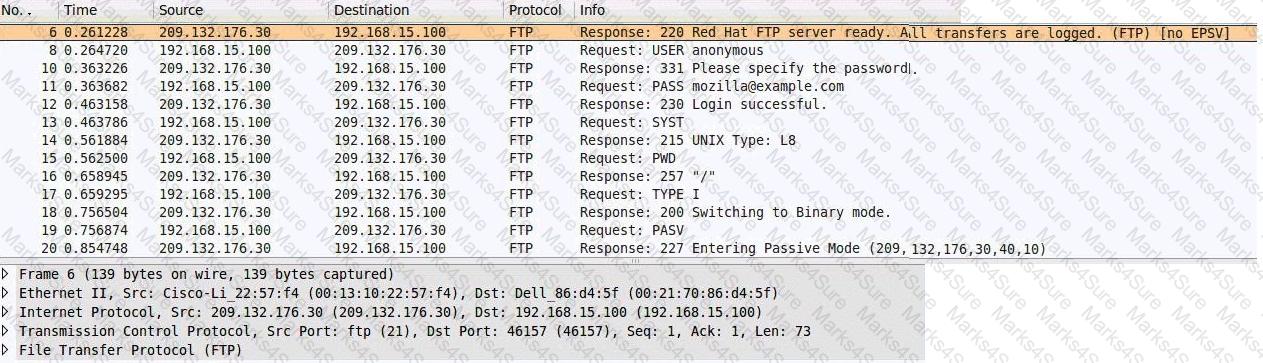
Which of the following best describes the protocol used, along with its primary benefit?
Which of the following activities is the most effective at keeping the actions of nae end users from putting the company ' s physical and logicalWhich of the following activities is the most effective at keeping the actions of na?e end users from putting the company ' s physical and logical resources at risk?
Requests for Web-based resources have become unacceptably slow. You have been assigned to implement a solution that helps solve this problem. Which of the following would you recommend?