CloudSec-Pro Palo Alto Networks Cloud Security Professional Questions and Answers
Which two required request headers interface with Prisma Cloud API? (Choose two.)
A customer wants to monitor the company’s AWS accounts via Prisma Cloud, but only needs the resource configuration to be monitored for now.
Which two pieces of information do you need to onboard this account? (Choose two.)
Which IAM Azure RQL query would correctly generate an output to view users who have sufficient permissions to create security groups within Azure AD and create applications?
Under which tactic is “Exploit Public-Facing Application” categorized in the ATT & CK framework?
What should be used to associate Prisma Cloud policies with compliance frameworks?
A customer finds that an open alert from the previous day has been resolved. No auto-remediation was configured.
Which two reasons explain this change in alert status? (Choose two.)
During an initial deployment of Prisma Cloud Compute, the customer sees vulnerabilities in their environment.
Which statement correctly describes the default vulnerability policy?
A user from an organization is unable to log in to Prisma Cloud Console after having logged in the previous day.
Which area on the Console will provide input on this issue?
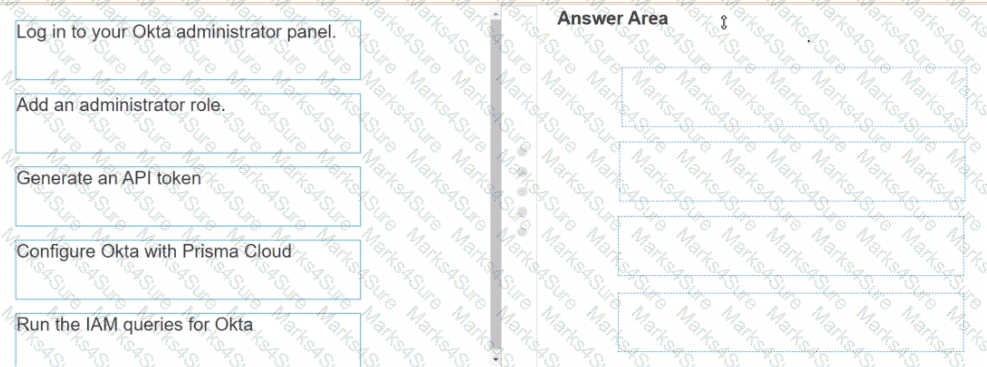
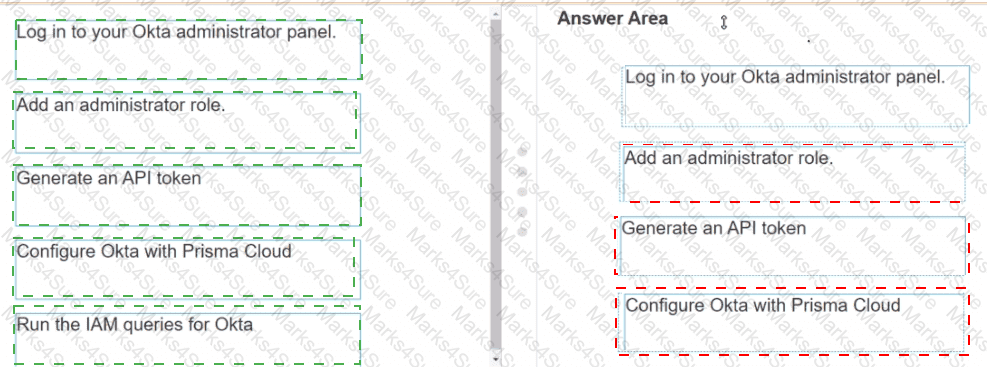
Put the steps of integrating Okta with Prisma Cloud in the right order in relation to CIEM or SSO okra integration.
What improves product operationalization by adding visibility into feature utilization and missed opportunities?
Which two statements explain differences between build and run config policies? (Choose two.)
The Prisma Cloud administrator has configured a new policy.
Which steps should be used to assign this policy to a compliance standard?
Which action would be applicable after enabling anomalous compute provisioning?
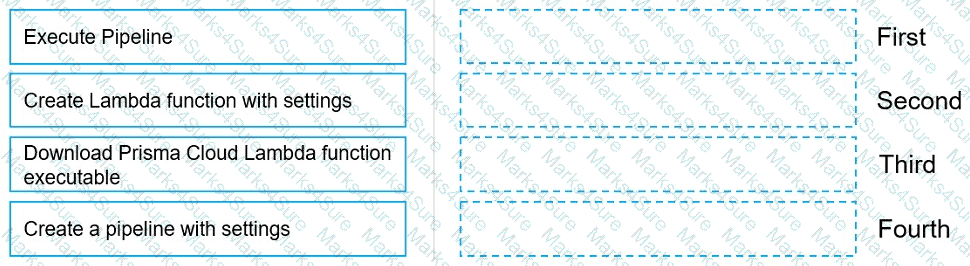
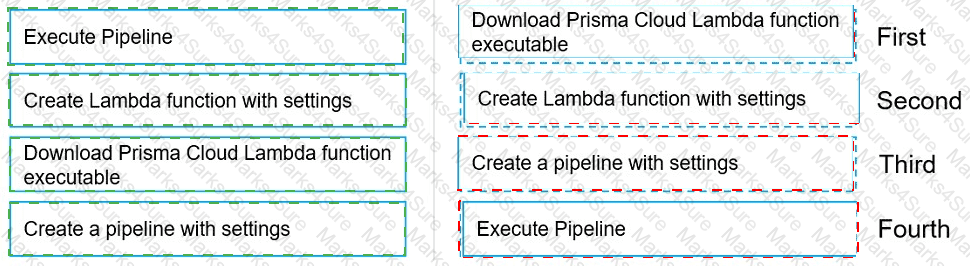
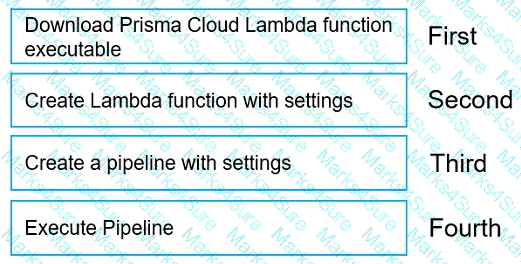
Move the steps to the correct order to set up and execute a serverless scan using AWS DevOps.
Which two frequency options are available to create a compliance report within the console? (Choose two.)
An administrator has a requirement to ingest all Console and Defender logs to Splunk.
Which option will satisfy this requirement in Prisma Cloud Compute?
The security team wants to enable the “block” option under compliance checks on the host.
What effect will this option have if it violates the compliance check?
Which resource and policy type are used to calculate AWS Net Effective Permissions? (Choose two.)
The compliance team needs to associate Prisma Cloud policies with compliance frameworks. Which option should the team select to perform this task?
An administrator of Prisma Cloud wants to enable role-based access control for Docker engine.
Which configuration step is needed first to accomplish this task?
Which two proper agentless scanning modes are supported with Prisma Cloud? (Choose two).
Which role must be assigned to DevOps users who need access to deploy Container and Host Defenders in Compute?
What is the correct method for ensuring key-sensitive data related to SSNs and credit card numbers cannot be viewed in Dashboard > Data view during investigations?
Prisma Cloud Compute has been installed on Onebox. After Prisma Cloud Console has been accessed. Defender is disconnected and keeps returning the error " No console connectivity " in the logs.
What could be causing the disconnection between Console and Defender in this scenario?
A security team notices a number of anomalies under Monitor > Events. The incident response team works with the developers to determine that these anomalies are false positives.
What will be the effect if the security team chooses to Relearn on this image?
Which three types of buckets exposure are available in the Data Security module? (Choose three.)
A customer has serverless functions that are deployed in multiple clouds.
Which serverless cloud provider is covered be “overly permissive service access” compliance check?
A customer has a requirement to scan serverless functions for vulnerabilities.
What is the correct option to configure scanning?
Which action must be taken to enable a user to interact programmatically with the Prisma Cloud APIs and for a nonhuman entity to be enabled for the access keys?
Which three incident types will be reflected in the Incident Explorer section of Runtime Defense? (Choose three.)
What is the purpose of Incident Explorer in Prisma Cloud Compute under the " Monitor " section?
The security team wants to protect a web application container from an SQLi attack. Which type of policy should the administrator create to protect the container?
What is the function of the external ID when onboarding a new Amazon Web Services (AWS) account in Prisma Cloud?
An administrator sees that a runtime audit has been generated for a Container. The audit message is “DNS resolution of suspicious name wikipedia.com. type A”.
Why would this message appear as an audit?
One of the resources on the network has triggered an alert for a Default Config policy.
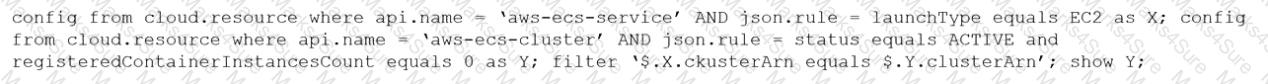
Given the following resource JSON snippet:
Which RQL detected the vulnerability?
A)
B)
C)
D)
An administrator has been tasked with a requirement by your DevSecOps team to write a script to continuously query programmatically the existing users, and the user’s associated permission levels, in a Prisma Cloud Enterprise tenant.
Which public documentation location should be reviewed to help determine the required attributes to carry out this step?
Which intensity setting for anomaly alerts is used for the measurement of 100 events over 30 days?
Which of the following are correct statements regarding the use of access keys? (Choose two.)
What will happen when a Prisma Cloud Administrator has configured agentless scanning in an environment that also has Host and Container Defenders deployed?
Which three Orchestrator types are supported when deploying Defender? (Choose three.)
Which two processes ensure that builds can function after a Console upgrade? (Choose two.)
A security team is deploying Cloud Native Application Firewall (CNAF) on a containerized web application. The application is running an NGINX container. The container is listening on port 8080 and is mapped to host port 80.
Which port should the team specify in the CNAF rule to protect the application?
Which statement is true about obtaining Console images for Prisma Cloud Compute Edition?
Which API calls can scan an image named myimage: latest with twistcli and then retrieve the results from Console?
Which command correctly outputs scan results to stdout in tabular format and writes scan results to a JSON file while still sending the results to Console?
An administrator for Prisma Cloud needs to obtain a graphical view to monitor all connections, including connections across hosts and connections to any configured network objects.
Which setting does the administrator enable or configure to accomplish this task?
An administrator wants to retrieve the compliance policies for images scanned in a continuous integration (CI) pipeline.
Which endpoint will successfully execute to enable access to the images via API?
What is the maximum number of access keys a user can generate in Prisma Cloud with a System Admin role?
A customer wants to harden its environment from misconfiguration.
Prisma Cloud Compute Compliance enforcement for hosts covers which three options? (Choose three.)
What is an automatically correlated set of individual events generated by the firewall and runtime sensors to identify unfolding attacks?
Which type of compliance check is available for rules under Defend > Compliance > Containers and Images > CI?
Which file extension type is supported for Malware scanning in Prisma Cloud Data Security (PCDS)?
The development team is building pods to host a web front end, and they want to protect these pods with an application firewall.
Which type of policy should be created to protect this pod from Layer7 attacks?
Given the following audit event activity snippet:
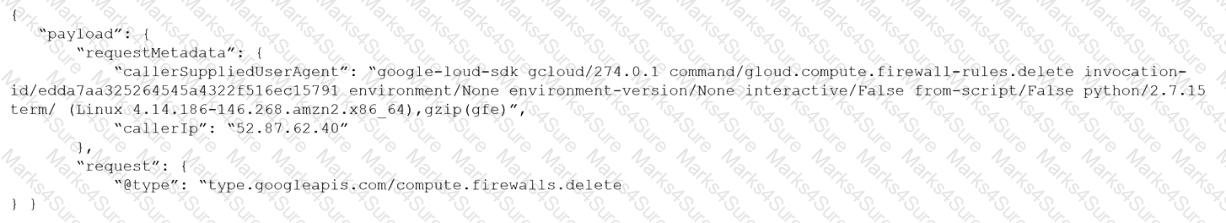
Which RQL will be triggered by the audit event?
A)
B)
C)
D)
You are an existing customer of Prisma Cloud Enterprise. You want to onboard a public cloud account and immediately see all of the alerts associated with this account based off ALL of your tenant’s existing enabled policies. There is no requirement to send alerts from this account to a downstream application at this time.
Which option shows the steps required during the alert rule creation process to achieve this objective?
A container and image compliance rule has been configured by enabling all checks; however, upon review, the container ' s compliance view reveals only the entries in the image below.
What is the appropriate action to take next?
Which command should be used in the Prisma Cloud twistcli tool to scan the nginx:latest image for vulnerabilities and compliance issues?
A)
B)
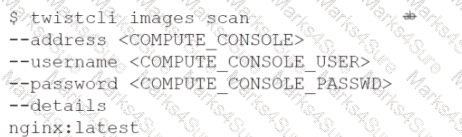
C)
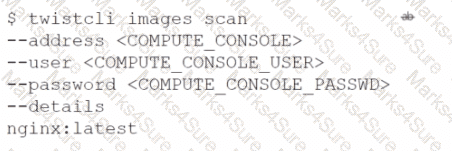
D)
In Prisma Cloud for Azure Net Effective Permissions Calculation, the following Azure permission levels are supported by which three permissions? (Choose three).
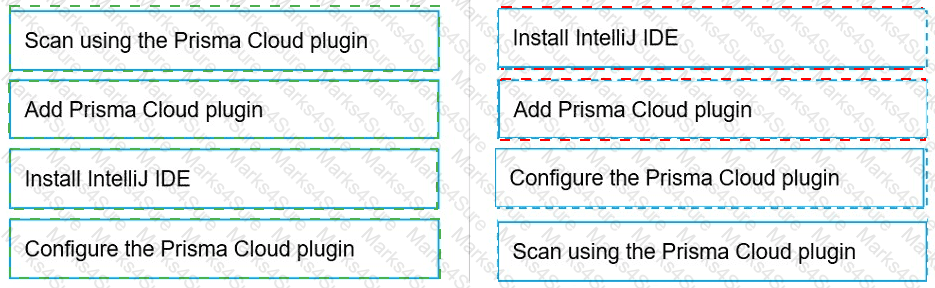
Put the steps involved to configure and scan using the IntelliJ plugin in the correct order.
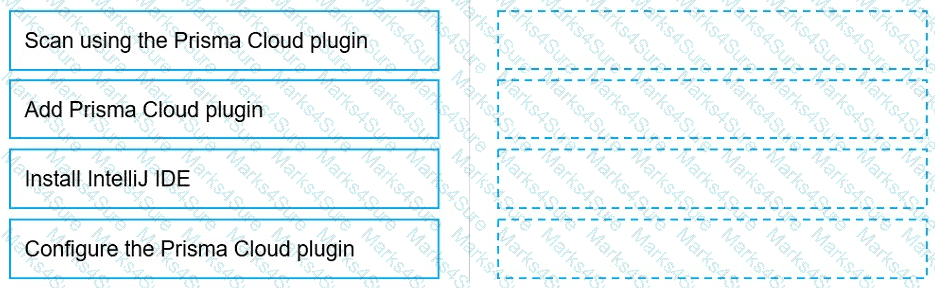

 Graphical user interface, text, application Description automatically generated
Graphical user interface, text, application Description automatically generated