Is this a supported user authentication method for Universal Control Plane?
Solution.x.500
Is this a way to configure the Docker engine to use a registry without a trusted TLS certificate?
Solution: List insecure registries in the ' daemon.json configuration file under the \insecure-registries ' key.
Will this command mount the host ' s ' /data ' directory to the ubuntu container in read-only mode?
Solution: ' docker run --volume /data:/mydata:ro ubuntu '
One of several containers in a pod is marked as unhealthy after failing its livenessProbe many times. Is this the action taken by the orchestrator to fix the unhealthy container?
Solution: The controller managing the pod is autoscaled back to delete the unhealthy pod and alleviate load.
In the context of a swarm mode cluster, does this describe a node?
Solution: a physical machine participating in the swarm
You are pulling images from a Docker Trusted Registry installation
configured to use self-signed certificates, and this error appears:
`x509: certificate signed by unknown authority.
You already downloaded the Docker Trusted Registry certificate authority
certificate from https://dtr.example.com/ca.
How do you trust it? (Select two.)
The Kubernetes yaml shown below describes a clusterIP service.
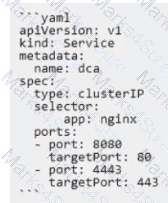
Is this a correct statement about how this service routes requests?
Solution: Traffic sent to the IP of this service on port 80 will be routed to port 8080 in a random pod with the label app:
nginx.
Does this command create a swarm service that only listens on port 53 using the UDP protocol?
Solution: ‘docker service create -name dns-cache -p 53:53 -service udp dns-cache '
Will this command ensure that overlay traffic between service tasks is encrypted?
Solution:docker service create --network --secure
During development of an application meant to be orchestrated by Kubemetes, you want to mount the /data directory on your laptop into a container.
Will this strategy successfully accomplish this?
Solution. Create a Persistent VolumeClaim requesting storageClass:”” (which defaults to local storage) and hostPath: /data, and use this to populate a volume in a pod.
You set up an automatic pruning policy on a DTR repository to prune all images using Apache licenses.
What effect does this have on images in this repository?
Can this set of commands identify the published port(s) for a container?
Solution: docker container inspect ' , ' docker port '
Is this the purpose of Docker Content Trust?
Solution.Indicate an image on Docker Hub is an official image.
Two development teams in your organization use Kubernetes and want to deploy their applications while ensuring that Kubernetes-specific resources, such as secrets, are grouped together for each application.
Is this a way to accomplish this?
Solution: Create one namespace for each application and add all the resources to it.
Seven managers are in a swarm cluster.
Is this how should they be distributed across three datacenters or availability zones?
Solution: 3-3-1
You created a new service named ' http* and discover it is not registering as healthy. Will this command enable you to view the list of historical tasks for this service?
Solution. ‘docker inspect http "
Is this an advantage of multi-stage builds?
Solution: better caching when building Docker images
Will this command display a list of volumes for a specific container?
Solution:docker volume inspect nginx '
Is this a function of UCP?
Solution: enforces the deployment of signed images to the cluster
Will this action upgrade Docker Engine CE to Docker Engine EE?
Solution: Uninstall ' docker-ce ' package before installing ' docker-ee ' package.
In the context of a swarm mode cluster, does this describe a node?
Solution: an instance of the Docker engine participating in the swarm
You configure a local Docker engine to enforce content trust by setting the environment variable DOCKER_C0NTENT_TRUST=l. If myorg/myimage: 1.0 is unsigned, does Docker block this command?
Solution.docker image build, from a Dockeflle that begins FROM myorg/myimage: l1.0
Is this a Linux kernel namespace that is disabled by default and must be enabled at Docker engine runtime to be used?
Solution.pid
You created a new service named ' http ' and discover it is not registering as healthy. Will this command enable you to view the list of historical tasks for this service?
Solution: ' docker inspect http '
Will this command ensure that overlay traffic between service tasks is encrypted?
Solution:docker network create -d overlay --secure
Is this the purpose of Docker Content Trust?
Solution: Verify and encrypt Docker registry TLS.
Is this a type of Linux kernel namespace that provides container isolation?
Solution.Process ID
During development of an application meant to be orchestrated by Kubernetes, you want to mount the /data directory on your laptop into a container.
Will this strategy successfully accomplish this?
Solution: Create a PersistentVolume with storageciass: " " and hostPath: /data, and a persistentVolumeClaim requesting this PV. Then use that PVC to populate a volume in a pod
Will this command display a list of volumes for a specific container?
Solution. ‘docker container logs nginx –volumes’
Will this configuration achieve fault tolerance for managers in a swarm?
Solution: one manager node for two worker nodes
Does this command create a swarm service that only listens on port 53 using the UDP protocol?
Solution. ‘docker service create -name dns-cache -p 53:53 -constraint networking.protocol.udp=true dns-cache "
Are these conditions sufficient for Kubernetes to dynamically provision a persistentVolume, assuming there are no limitations on the amount and type of available external storage?
Solution: A volume is defined in a pod specification with the key persistentVolume: default.
Does this command display all the pods in the cluster that are labeled as env; development ' ?
Solution. ‘kubectl gel pods --all-namespaces -I ' env in (development) ' '
You want to create a container that is reachable from its host ' s network.
Does this action accomplish this?
Solution.Use either EXPOSE or -publish to access the container on the bridge network.
In Docker Trusted Registry, is this how a user can prevent an image, such as ' nginx:latest’, from being overwritten by another user with push access to the repository?
Solution: Use the DTR web Ul to make all tags in the repository immutable.
You want to create a container that is reachable from its host ' s network.
Does this action accomplish this?
Solution.Use network connect to access the container on the bridge network.
An application image runs in multiple environments, with each environment using different certificates and ports.
Is this a way to provision configuration to containers at runtime?
Solution: Create a Dockerfile for each environment, specifying ports and ENV variables for certificates.
Will this sequence of steps completely delete an image from disk in the Docker Trusted Registry?
Solution: Manually delete all layers used by the image on the disk from the Docker Trusted Registry.
Will this command ensure that overlay traffic between service tasks is encrypted?
Solution: docker network create -d overlay -o encrypted=true < network-name >
Does this command display all the pods in the cluster that are labeled as ' env: development ' ?
Solution: ' kubectl get pods --all-namespaces -I env=development '
Is this statement correct?
Solution: A Dockerfile provides instructions for building a Docker image
One of several containers in a pod is marked as unhealthy after failing its livenessProbe many times. Is this the action taken by the orchestrator to fix the unhealthy container?
Solution: The unhealthy container is restarted.
A company ' s security policy specifies that development and production containers must run on separate nodes in a given Swarm cluster.
Can this be used to schedule containers to meet the security policy requirements?
Solution: node affinities
Does this command create a swarm service that only listens on port 53 using the UDP protocol?
Solution. ‘docker service create -name dns-cache -p 53:53 -udp dns-cache’
You are running only Kubernetes workloads on a worker node that requires
maintenance, such as installing patches or an OS upgrade.
Which command must be run on the node to gracefully terminate all pods on
the node, while marking the node as unschedulable?
Is this a supported user authentication method for Universal Control Plane?
Solution.SAML
You created a new service named ' http ' and discover it is not registering as healthy. Will this command enable you to view the list of historical tasks for this service?
Solution: ' docker service ps http '
Will This command list all nodes in a swarm cluster from the command line?
Solution. ‘docker swarm nodes '
Two development teams in your organization use Kubernetes and want to deploy their applications while ensuring that Kubernetes-specific resources, such as secrets, are grouped together for each application.
Is this a way to accomplish this?
Solution. Create a collection for for each application.
Which networking drivers allow you to enable multi-host network connectivity
between containers?
A Kubernetes node is allocated a /26 CIDR block (64 unique IPs) for its
address space.
If every pod on this node has exactly two containers in it, how many pods can
this address space support on this node?
You configure a local Docker engine to enforce content trust by setting the environment variable
DOCKER_CONTENT_TRUST=1.
If myorg/myimage: 1.0 is unsigned, does Docker block this command?
Solution: docker service create myorg/myimage:1.0
Is this a type of Linux kernel namespace that provides container isolation?
Solution: Network