John works as a professional Ethical Hacker. He is assigned a project to test the security of www.abc.com. You have searched all open ports of the ABC server. Now, you want to perform the next information-gathering step, i.e., passive OS fingerprinting.
Which of the following tools can you use to accomplish the task?
You work as a System Administrator for ABC Inc. The company has a Linux-based network. You are a root user on the Red Hat operating system. Your network is configured for IPv6 IP addressing.
Which of the following commands will you use to test TCP/IP connectivity?
Which of the following statements about a host-based intrusion prevention system (HIPS) are true?
Each correct answer represents a complete solution. (Choose two.)
Which of the following algorithms is used as a default algorithm for ESP extension header in IPv6?
You work as a Network Administrator for Net Perfect Inc. The company has a Windows Server 2008 network environment. The network is configured as a Windows Active Directory-based single forest single domain network. The network is configured on IP version 6 protocol. All the computers on the network are connected to a switch device. One day, users complain that they are unable to connect to a file server. You try to ping the client computers from the server, but the pinging fails. You try to ping the server ' s own loopback address, but it fails to ping. You restart the server, but the problem persists.
What is the most likely cause?
Which of the following statements about Access control list (ACL) are true?
Each correct answer represents a complete solution. (Choose three.)
Which of the following group management messages is used by routers to handle the IPv6 multicast routing?
Which of the following statements about segmentation of a network using router is true?
Each correct answer represents a complete solution. (Choose three.)
You work as a Network Administrator for ABC Inc. You want to configure Snort as an IDS for your company ' s wireless network, but you are concerned that Snort does not support all types of traffic.
What traffic does Snort support?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following tools detects certain types of packet filters and NAT setups?
Jain works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.abc.com.
He has successfully completed the following steps of the preattack phase:
> > Information gathering
> > Determining network range
> > Identifying active machines
> > Finding open ports and applications
> > OS fingerprinting
> > Fingerprinting services
Now Jain wants to perform network mapping of the ABC network.
Which of the following tools can he use to accomplish his task?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following devices works as a transparent bridge between the wireless clients and the wired network?
Which of the following Intrusion Detection Systems (IDS) is used to monitor rogue access points and the use of wireless attack tools?
Which of the following statements are true about the Network Honeypot a rulebase?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following Wireless LAN standard devices is least affected by interference from domestic appliances such as microwave ovens?
You work as a Network Administrator for Net Perfect Inc. The company has a TCP/IP network. You have been assigned a task to configure security mechanisms for the network of the company. You have decided to configure a packet filtering firewall.
Which of the following may be the reasons that made you choose a packet filtering firewall as a security mechanism?
Each correct answer represents a complete solution. (Choose all that apply.)
Jain works as a professional Ethical Hacker. He has been assigned a project for testing the security of www.abc.com.
He wants to corrupt an IDS signature database so that performing attacks on the server is made easy and he can observe the flaws in the ABC server.
To perform his task, he first of all sends a virus that continuously changes its signature to avoid detection from IDS. Since the new signature of the virus does not match the old signature, which is entered in the IDS signature database, IDS becomes unable to point out the malicious virus.
Which of the following IDS evasion attacks is John performing?
Which of the following commands is recommended by Cisco for latest switches and routers to erase the contents of NVRAM?
You work as a Network Administrator for ABC Inc. The company has a TCP/IP network. You have been assigned a task to configure a stateful packet filtering firewall to secure the network of the company. You are encountering some problems while configuring the stateful packet filtering firewall.
Which of the following can be the reasons for your problems?
Each correct answer represents a complete solution. (Choose all that apply.)
You work as a Network Administrator for a bank. For securing the bank ' s network, you configure a firewall and an IDS. In spite of these security measures, intruders are able to attack the network. After a close investigation, you find that your IDS is not configured properly and hence is unable to generate alarms when needed.
What type of response is the IDS giving?
Which of the following firewalls operates at three layers - Layer3, Layer4, and Layer5?
You work as a technician for ABC Inc. You are troubleshooting a connectivity issue on a network. You are using the ping command to verify the connectivity between two hosts. You want ping to send larger sized packets than the usual 32-byte ones.
Which of the following commands will you use?
Address Resolution Protocol (ARP) spoofing, also known as ARP poisoning or ARP Poison Routing (APR), is a technique used to attack an Ethernet wired or wireless network. ARP spoofing may allow an attacker to sniff data frames on a local area network (LAN), modify the traffic, or stop the traffic altogether. The principle of ARP spoofing is to send fake ARP messages to an Ethernet LAN.
What steps can be used as a countermeasure of ARP spoofing?
Each correct answer represents a complete solution. (Choose all that apply.)
On which of the following interfaces of the router is the clock rate command used?
Which of the following is an intrusion detection system that reads all incoming packets and tries to find suspicious patterns known as signatures or rules?
Which of the following types of firewall ensures that the packets are part of the established session?
Which of the following techniques correlates information found on multiple hard drives?
You work as a Security Manager for Tech Perfect Inc. The company has a Windows-based network. You want to scroll real-time network traffic to a command console in a readable format.
Which of the following command line utilities will you use to accomplish the task?
You work as a Network Administrator for NetTech Inc. You want to prevent your network from Ping flood attacks.
Which of the following protocols will you block to accomplish this task?
Which of the following is a Cisco IOS management term described in the statement below?
" It is the fourth digit in the configuration register and contains a hexadecimal value. The bootstrap program uses its value to choose which operating system to load into RAM " .
Adam has installed and configured his wireless network. He has enabled numerous security features such as changing the default SSID, enabling WPA encryption, and enabling MAC filtering on his wireless router. Adam notices that when he uses his wireless connection, the speed is sometimes 16 Mbps and sometimes it is only 8 Mbps or less. Adam connects to the management utility wireless router and finds out that a machine with an unfamiliar name is connected through his wireless connection. Paul checks the router ' s logs and notices that the unfamiliar machine has the same MAC address as his laptop.
Which of the following attacks has been occurred on the wireless network of Adam?
The general form of the Cisco IOS is a.b.c.de.
Which of the following indicates the major version number of the Cisco IOS?
WinDump, tcpdump, and Wireshark specify which fields of information libpcap should record.
Which of the following filters do they use in order to accomplish the task?
The promiscuous mode is a configuration of a network card that makes the card pass all traffic it receives to the central processing unit rather than just packets addressed to it.
Which of the following tools works by placing the host system network card into the promiscuous mode?
Which of the following tools performs comprehensive tests against web servers for multiple items, including over 6100 potentially dangerous files/CGIs?
The simplest form of a firewall is a packet filtering firewall. Typically, a router works as a packet-filtering firewall and has the capability to filter on some of the contents of packets.
On which of the following layers of the Open System Interconnection (OSI) reference model do these routers filter information?
Each correct answer represents a complete solution. (Choose all that apply.)
An organization has more than a couple of external business, and exchanges dynamic routing information with the external business partners. The organization wants to terminate all routing from a partner at an edge router, preferably receiving only summary routes from the partner.
Which of the following will be used to change all partner addresses on traffic into a range of locally assigned addresses?
Which of the following tools uses PDA and barcode technologies in order to enable effective identification, control, and reporting of items in a site?
Which of the following can be used in an extended access list to filter traffic?
Each correct answer represents a part of the solution. (Choose all that apply.)
Which of the following techniques is used to identify attacks originating from a botnet?
You work as a Network Architect for Tech Perfect Inc. The company has a corporate LAN network. You will have to perform the following tasks:
• Limit events that occur from security threats such as viruses, worms, and spyware.
• Restrict access to the network based on identity or security posture.
Which of the following services will you deploy in the network to accomplish the tasks?
Which of the following devices is used to identify out-of-date software versions, applicable patches, system upgrades, etc?
Which of the following types of firewall functions by creating two different communications, one between the client and the firewall, and the other between the firewall and the end server?
Which of the following is an attack with IP fragments that cannot be reassembled?
Which of the following honeypots is a low-interaction honeypot and is used by companies or corporations for capturing limited information about malicious hackers?
Which of the following firewalls filters the traffic based on the header of the datagram?
Which of the following wireless security features provides the best wireless security mechanism?
You work as a Network Administrator for Tech Perfect Inc. You are required to verify security policies configured in the company ' s networks.
Which of the following applications will you use to accomplish the task?
Which of the following fields are specified when rules are created for the Network Honeypot rulebase?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following methods is used by forensic investigators to acquire an image over the network in a secure manner?
SSH is a network protocol that allows data to be exchanged between two networks using a secure channel.
Which of the following encryption algorithms can be used by the SSH protocol?
Each correct answer represents a complete solution. (Choose all that apply.)
Secure Shell (SSH) is a network protocol that allows data to be exchanged using a secure channel between two networked devices.
Which of the following features are supported by Secure Shell?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following hexadecimal values in the boot field in the configuration register loads the first IOS file found in Flash memory?
Which of the following techniques allows probing firewall rule-sets and finding entry points into the targeted system or network?
Which of the following forms on NAT maps multiple unregistered IP addresses to a single registered IP address by using different ports?
An attacker changes the address of a sub-routine in such a manner that it begins to point to the address of the malicious code. As a result, when the function has been exited, the application can be forced to shift to the malicious code. The image given below explains this phenomenon:
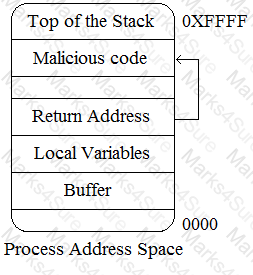
Which of the following tools can be used as a countermeasure to such an attack?
You work as a professional Computer Hacking Forensic Investigator for DataEnet Inc. You want to investigate e-mail information of an employee of the company. The suspected employee is using an online e-mail system such as Hotmail or Yahoo.
Which of the following folders on the local computer will you review to accomplish the task?
Each correct answer represents a complete solution. (Choose all that apply.)
You are the Network Administrator for a college. Wireless access is widely used at the college. You want the most secure wireless connections you can have.
Which of the following would you use?
Sam works as a Security Manager for ABC Inc. The company has a Windows-based network. Sam wants to prevent specific traffic from IDP processing in order to reduce false positives.
Which of the following rulebases will he use to accomplish the task?
You work as a Network Security Administrator for NetPerfect Inc. The company has a Windowsbased network. You are in charge of the data and network security of the company. While performing a threat log analysis, you observe that one of the database administrators is pilfering confidential data.
What type of threat is this?
Which of the following intrusion detection systems (IDS) produces the false alarm because of the abnormal behavior of users and network?
Jain works as a Security Manager for ABC Inc. The company has a Windows-based network.
Jain has been assigned a project to detect the services used by an attack to access the network. For this purpose, he is required to use the predefined service objects of the rulebase. This predefined service object defines the services used in the attack to access the network.
Which of the following objects will he create when he finds that the attack is not defined in the predefined service objects?
Which of the following attacks can be mitigated by providing proper training to the employees in an organization?
Session splicing is an IDS evasion technique in which an attacker delivers data in multiple small-sized packets to the target computer. Hence, it becomes very difficult for an IDS to detect the attack signatures of such attacks.
Which of the following tools can be used to perform session splicing attacks?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following statements about an IDP rule base notification are true?
Which of the following security protocols uses a single, manually configured, static key for data encryption that is shared by the client and the WAP?
You send and receive messages on Internet. A man-in-the-middle attack can be performed to capture and read your message.
Which of the following Information assurance pillars ensures the security of your message or data against this type of attack?
Which of the following types of Intrusion Detection Systems consists of an agent on a host that identifies intrusions by analyzing system calls, application logs, file-system modifications (binaries, password files, capability/acl databases) and other host activities and state?
Which of the following is a version of netcat with integrated transport encryption capabilities?
Which of the following vulnerability scanners detects vulnerabilities by actually performing attacks?
In which of the following IDS evasion techniques does an attacker deliver data in multiple small sized packets, which makes it very difficult for an IDS to detect the attack signatures of such attacks?
Andrew works as a Forensic Investigator for PassGuide Inc. The company has a Windows-based environment. The company ' s employees use Microsoft Outlook Express as their e-mail client program. E-mails of some employees have been deleted due to a virus attack on the network. Andrew is therefore assigned the task to recover the deleted mails.
Which of the following tools can Andrew use to accomplish the task?
Each correct answer represents a complete solution. (Choose two.)
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He wants to send malicious data packets in such a manner that one packet fragment overlaps data from a previous fragment so that he can perform IDS evasion on the We-are-secure server and execute malicious data.
Which of the following tools can he use to accomplish the task?
You work as a technician for Tech Perfect Inc. You are troubleshooting an Internet name resolution issue. You ping your ISP ' s DNS server address and find that the server is down. You want to continuously ping the DNS address until you have stopped the command.
Which of the following commands will you use?
In which of the following situations does legal and authorized traffic cause an intrusion detection system (IDS) to generate an alert and slow down performance?
Each correct answer represents a complete solution. (Choose all that apply.)
Which of the following files is a Cisco IOS configuration file that resides in RAM?