A customer has a requirement to scan serverless functions for vulnerabilities.
What is the correct option to configure scanning?
Which two statements are true about the differences between build and run config policies? (Choose two.)
Which three AWS policy types and identities are used to calculate the net effective permissions? (Choose three).
A customer finds that an open alert from the previous day has been resolved. No auto-remediation was configured.
Which two reasons explain this change in alert status? (Choose two.)
Which three actions are required in order to use the automated method within Azure Cloud to streamline the process of using remediation in the identity and access management (IAM) module? (Choose three.)
The compliance team needs to associate Prisma Cloud policies with compliance frameworks. Which option should the team select to perform this task?
What is the correct method for ensuring key-sensitive data related to SSNs and credit card numbers cannot be viewed in Dashboard > Data view during investigations?
A customer has a requirement to automatically protect all Lambda functions with runtime protection. What is the process to automatically protect all the Lambda functions?
Which of the following are correct statements regarding the use of access keys? (Choose two.)
When would a policy apply if the policy is set under Defend > Vulnerability > Images > Deployed?
The InfoSec team wants to be notified via email each time a Security Group is misconfigured. Which Prisma Cloud tab should you choose to complete this request?
What is the function of the external ID when onboarding a new Amazon Web Services (AWS) account in Prisma Cloud?
Which two of the following are required to be entered on the IdP side when setting up SSO in Prisma Cloud? (Choose two.)
Which role must be assigned to DevOps users who need access to deploy Container and Host Defenders in Compute?
A Systems Engineer is the administrator of a self-hosted Prisma Cloud console. They upgraded the console to the latest version. However, after the upgrade, the console does not show all the policies configured. Before they upgraded the console, they created a backup manually and exported it to a local drive. Now they have to install a Prisma Cloud to restore from the backup that they manually created. Which Prisma Cloud version can they can restore with the backup?
Prisma Cloud supports sending audit event records to which three targets? (Choose three.)
What will happen when a Prisma Cloud Administrator has configured agentless scanning in an environment that also has Host and Container Defenders deployed?
Which of the below actions would indicate – “The timestamp on the compliance dashboard?
An administrator sees that a runtime audit has been generated for a host. The audit message is:
“Service postfix attempted to obtain capability SHELL by executing /bin/sh /usr/libexec/postfix/postfix- script.stop. Low severity audit, event is automatically added to the runtime model”
Which runtime host policy rule is the root cause for this runtime audit?
A customer wants to be notified about port scanning network activities in their environment. Which policy type detects this behavior?
A Prisma Cloud administrator is onboarding a single GCP project to Prisma Cloud. Which two steps can be performed by the Terraform script? (Choose two.)
Which resource and policy type are used to calculate AWS Net Effective Permissions? (Choose two.)
Which set of steps is the correct process for obtaining Console images for Prisma Cloud Compute Edition?
What is an automatically correlated set of individual events generated by the firewall and runtime sensors to identify unfolding attacks?
What should be used to associate Prisma Cloud policies with compliance frameworks?
A customer wants to monitor the company’s AWS accounts via Prisma Cloud, but only needs the resource configuration to be monitored for now.
Which two pieces of information do you need to onboard this account? (Choose two.)
Web-Application and API Security (WAAS) provides protection for which two protocols? (Choose two.)
How does assigning an account group to an administrative user on Prisma Cloud help restrict access to resources?
Which step should a SecOps engineer implement in order to create a network exposure policy that identifies instances accessible from any untrusted internet sources?
A user from an organization is unable to log in to Prisma Cloud Console after having logged in the previous day.
Which area on the Console will provide input on this issue?
The Prisma Cloud administrator has configured a new policy.
Which steps should be used to assign this policy to a compliance standard?
The security auditors need to ensure that given compliance checks are being run on the host. Which option is a valid host compliance policy?
Given the following audit event activity snippet:
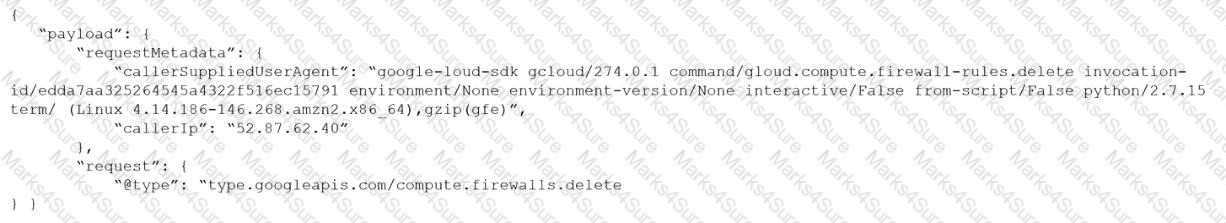
Which RQL will be triggered by the audit event?
A)
B)
C)
D)
Which two CI/CD plugins are supported by Prisma Cloud as part of its Code Security? (Choose two.)
Which two actions are required in order to use the automated method within Amazon Web Services (AWS) Cloud to streamline the process of using remediation in the identity and access management (IAM) module? (Choose two.)
A business unit has acquired a company that has a very large AWS account footprint. The plan is to immediately start onboarding the new company’s AWS accounts into Prisma Cloud Enterprise tenant immediately. The current company is currently not using AWS Organizations and will require each account to be onboarded individually.
The business unit has decided to cover the scope of this action and determined that a script should be written to onboard each of these accounts with general settings to gain immediate posture visibility across the accounts.
Which API endpoint will specifically add these accounts into the Prisma Cloud Enterprise tenant?
Which two integrated development environment (IDE) plugins are supported by Prisma Cloud as part of its Code Security? (Choose two.)
A customer has a development environment with 50 connected Defenders. A maintenance window is set for Monday to upgrade 30 stand-alone Defenders in the development environment, but there is no maintenance window available until Sunday to upgrade the remaining 20 stand-alone Defenders.
Which recommended action manages this situation?
What must be created in order to receive notifications about alerts generated when the operator is away from the Prisma Cloud Console?
The security team wants to enable the “block” option under compliance checks on the host.
What effect will this option have if it violates the compliance check?
Which ROL query is used to detect certain high-risk activities executed by a root user in AWS?
Which component of a Kubernetes setup can approve, modify, or reject administrative requests?
If you are required to run in an air-gapped environment, which product should you install?
On which cloud service providers can you receive new API release information for Prisma Cloud?
During an initial deployment of Prisma Cloud Compute, the customer sees vulnerabilities in their environment.
Which statement correctly describes the default vulnerability policy?
In WAAS Access control file upload controls, which three file types are supported out of the box? (Choose three.)
Given the following JSON query:
$.resource[*].aws_s3_bucket exists
Which tab is the correct place to add the JSON query when creating a Config policy?
When configuring SSO how many IdP providers can be enabled for all the cloud accounts monitored by Prisma Cloud?
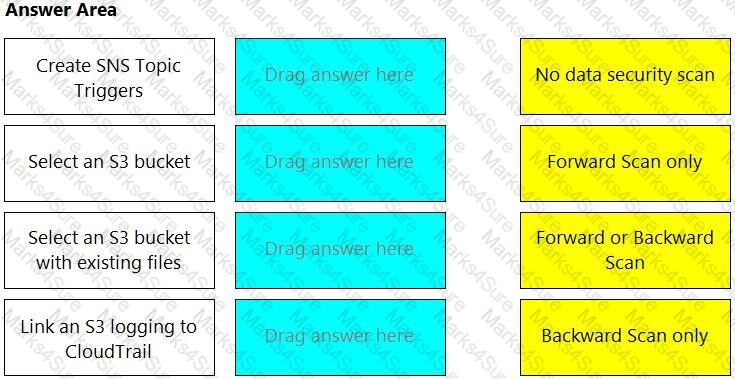
Match the correct scanning mode for each given operation.
(Select your answer from the pull-down list. Answers may be used more than once or not at all.)
A Prisma Cloud Administrator onboarded an AWS cloud account with agentless scanning enabled successfully to Prisma Cloud. Which item requires deploying defenders to be able to inspect the risk on the onboarded AWS account?
Which two statements explain differences between build and run config policies? (Choose two.)
The security team wants to target a CNAF policy for specific running Containers. How should the administrator scope the policy to target the Containers?
What is the most reliable and extensive source for documentation on Prisma Cloud APIs?
The development team is building pods to host a web front end, and they want to protect these pods with an application firewall.
Which type of policy should be created to protect this pod from Layer7 attacks?
Which two frequency options are available to create a compliance report within the console? (Choose two.)
What is the maximum number of access keys a user can generate in Prisma Cloud with a System Admin role?
An administrator has added a Cloud account on Prisma Cloud and then deleted it.
What will happen if the deleted account is added back on Prisma Cloud within a 24-hour period?
Creation of a new custom compliance standard that is based on other individual custom compliance standards needs to be automated.
Assuming the necessary data from other standards has been collected, which API order should be used for this new compliance standard?
Which two elements are included in the audit trail section of the asset detail view? (Choose two).
Which three steps are involved in onboarding an account for Data Security? (Choose three.)
The Unusual protocol activity (Internal) network anomaly is generating too many alerts. An administrator has been asked to tune it to the option that will generate the least number of events without disabling it entirely.
Which strategy should the administrator use to achieve this goal?
Which action must be taken to enable a user to interact programmatically with the Prisma Cloud APIs and for a nonhuman entity to be enabled for the access keys?
An administrator wants to retrieve the compliance policies for images scanned in a continuous integration (CI) pipeline.
Which endpoint will successfully execute to enable access to the images via API?