Which Panorama operational mode is necessary to manage a large number of firewalls and also act as a log collector?
Which firewall interface type allows you to non-disruptively monitor traffic coming from a port operating in promiscuous mode?
A firewall that was previously connected lo a User-ID agent server now shows disconnected What is the likely cause?
Which two types of security profiles are recommended to protect against known and unknown threats? (Choose two)
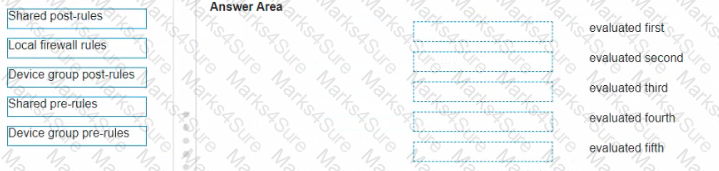
In Panorama the web interface displays the security rules in evaluation order Organize the security rules m the order in which they will be evaluated?
Which GlobalProtect feature ensures that only trusted endpoints can connect to the network?
An administrator needs to create a new Antivirus Profile to address a virus that is spreading internally over SMB.
To create a secure posture the administrator should choose which set of actions for the SMB decoder in an Antivirus Profile?
An existing customer who has deployed several Palo Alto Networks Next-Generation Firewalls would like to start using Device-ID to obtain policy rule recommendations They have also purchased a Support license, a Threat license a URL Filtering license, and a WildFire license for each firewall
What additional license do they need to purchase"?
Which interface deployments support the Aggregate Ethernet Active configuration? (Choose three.)
A customer has a five-year-old firewall in production in the time since the firewall was installed, the IT team deleted unused security policies on a regular basis but they did not remove the address objects and groups that were part of these security policies.
What is the best way to delete all of the unused address objects on the firewall?
Which touting configuration should you recommend lo a customer who wishes lo actively use multiple pathways to the same destination?